The launch of the Freedom.gov domain by the US State Department in February 2026 marks a dangerous turning point in the history of cyber geopolitics. While outwardly disguised as an anti-censorship tool promoting the free flow of information, its processing core is an algorithmic weapon designed to maintain Silicon Valley's platform hegemony and shatter the digital borders of sovereign nations. Today's ultra-deep report from the Tekin Command Center debugs the technical and diplomatic dimensions of this project. Shockingly, the primary target
The quiet yet explosive launch of the Freedom.gov domain in February 2026 is the cyber equivalent of deploying ballistic missiles across the world's digital borders. Today's Tekin Analysis report is a ruthless, deep-dive autopsy of a project directly steered by the US State Department; a project proving that in the new economy, a hegemon's power is no longer measured by its aircraft carriers, but by the ability of its algorithms to penetrate independent global networks.
1. Debugging Freedom.gov: A Diplomatic Weapon Disguised as a Protocol
At the Presentation Layer, the project's landing page is decorated with idealistic slogans of "information freedom" and "digital human rights." However, at Tekin Garage, we never trust the User Interface (UI); we look strictly at the processing core and system architecture. Freedom.gov is a centralized platform, backed by government supercomputers, designed to bore encrypted, untraceable tunnels straight through the heart of other nations' sovereign networks.
1.1. Washington's Cyber Doctrine: From Kinetic War to Platform Hegemony
The US government has realized that controlling Data Flow is the ultimate geopolitical tool of the 21st century. This project is an aggressive attempt to preserve Silicon Valley's platform hegemony in an era where nations (from Europe to Asia) are rapidly building national intranets, sovereign data centers, and localized networks. Through this tool, America aims to lock global users inside its own information ecosystem (Google, Meta, X) and prevent catastrophic "Data Leakage" to rival platforms. This is not a human rights tool; it is a forced data pipeline routed straight to American servers.
📌 Strategic Checkpoint 1 (Tekin Command Center)
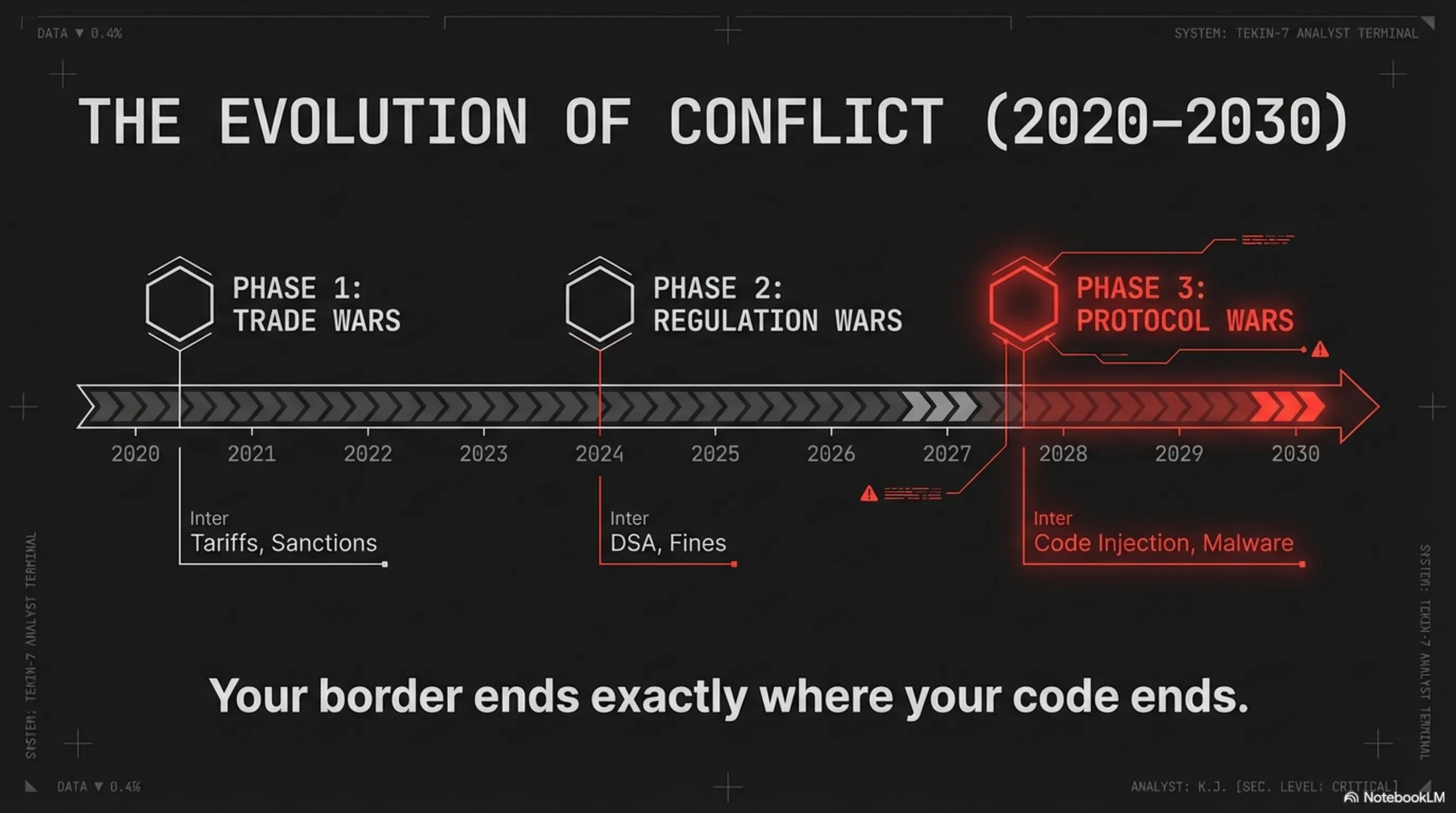
Project Freedom.gov proves that public diplomacy has completely mutated in 2026. Today, diplomacy is not about issuing political statements; it is about injecting encrypted protocols and policy-bypassing malware directly into the digital infrastructure of international rivals.
2. A Shot at the Heart of Brussels: Direct Confrontation with the EU's DSA
The most controversial, complex, and shocking dimension of this project—which led to the diplomatic postponement of its official unveiling at the Munich Security Conference—is not its targeting of authoritarian states, but its all-out confrontation with the European Union. In recent years, Europe has passed draconian legislation like the Digital Services Act (DSA) and the Digital Markets Act (DMA), forcing American tech giants to comply with local standards, censor specific content (under the guise of fighting fake news or hate speech), and pay multi-billion dollar fines.
2.1. The Regulatory War: When American Code Nullifies European Decrees
By developing Freedom.gov, Washington has sent a clear, brazen, cybernetic message to Brussels: "If you restrict our platforms through legislation, we will hand your citizens a direct tool to neutralize your regulatory authority." This platform effectively allows European users to tunnel securely outside EU jurisdiction and access content or services blocked by their own governments. This move is an aggressive, blatant violation of "European Digital Sovereignty." America is utilizing technological architecture to override the democratic laws of an entire union.
| Axis of Strategic Conflict | EU Approach (DSA Legislation) | US Doctrine (Freedom.gov Project) |
|---|---|---|
| Content Moderation & Censorship | Legal filtering, platform accountability | Bypassing local restrictions via encrypted clients |
| Data Sovereignty | Data localization, processing on EU soil | Forced tunneling & diverting data flow abroad |
| Geopolitical Authority | Legal Regulatory Power | Technological Hegemony & Cyber Infiltration |
📌 Strategic Checkpoint 2 (Tekin Command Center)
This unprecedented clash proves that in the new economy, the Regulation War is vastly more complex than traditional trade wars. Europe attempts to seize control via "legislative power," while America renders those laws entirely obsolete from the inside out via "coding power."
3. Network Technical Autopsy: Polymorphic Routing & the Fall of Firewalls
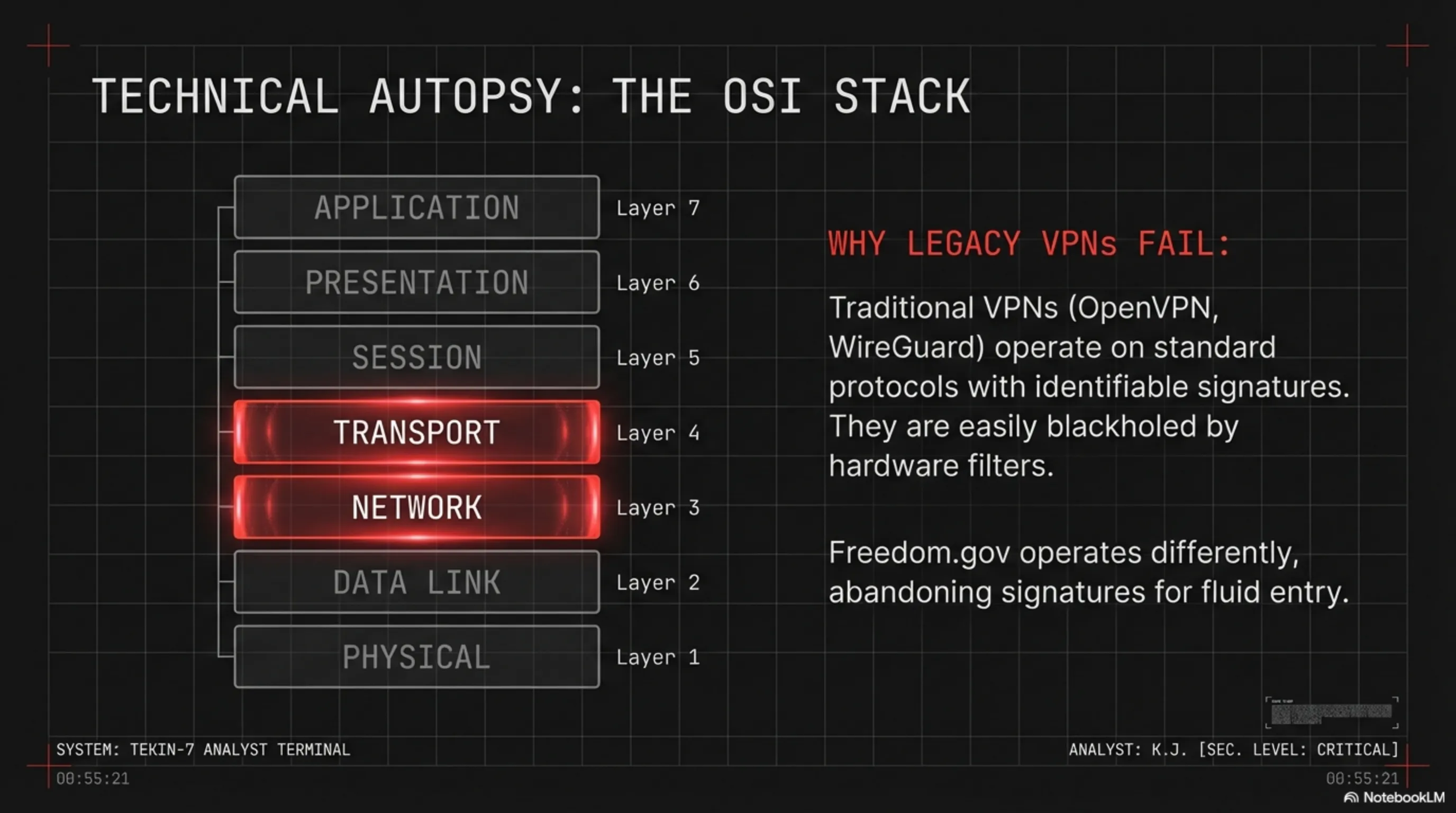
To understand the sheer depth of this weapon, we must autopsy its technical layers within the OSI model. Freedom.gov cannot be a simple VPN utilizing legacy protocols (like OpenVPN, IPSec, or WireGuard) because these possess distinct signatures and are easily blackholed by hardware-level filtering systems.
3.1. The Death of Deep Packet Inspection (DPI) Against AI Traffic Obfuscation
Deep network analysis by the Tekin Engineering Team indicates that an infrastructure on the scale of Freedom.gov absolutely relies on Polymorphic Routing and advanced Traffic Obfuscation techniques managed in real-time by Artificial Intelligence. This means that Data Packets dynamically mutate so that even the most advanced Deep Packet Inspection (DPI) systems cannot distinguish whether the traffic belongs to a circumvention tool, a 4K video stream, or a standard VoIP call.
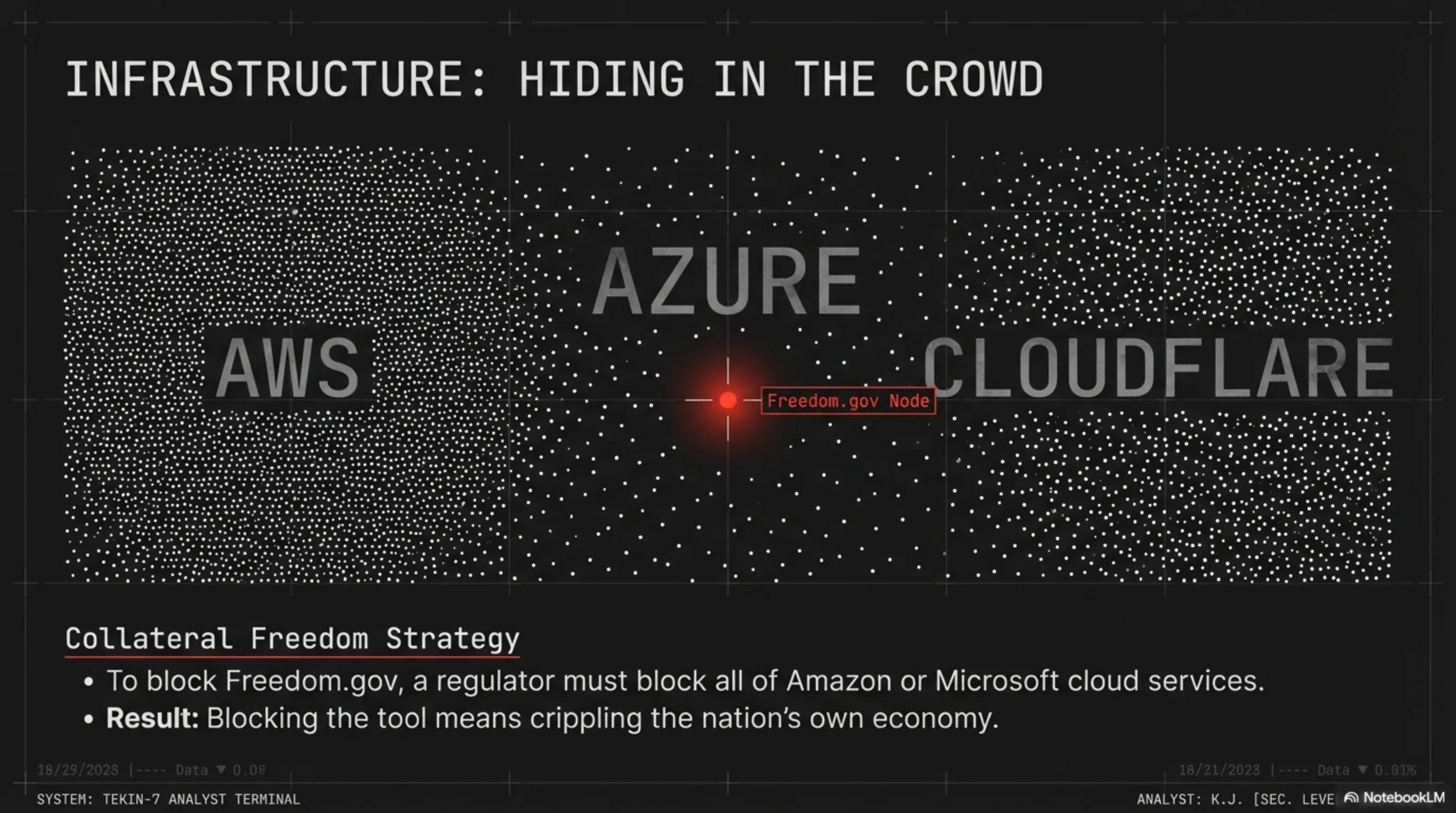
Furthermore, the system's architecture is highly likely built upon Decentralized Nodes scattered across hyperscale cloud infrastructures (like AWS, Azure, or Cloudflare). This "hiding in the crowd" approach makes IP-blocking the service practically impossible for regulators, unless they are willing to completely cripple their country's entire cloud internet traffic (a strategy known as Collateral Freedom).
📌 Strategic Checkpoint 3 (Tekin Command Center)
Neural network-driven traffic obfuscation has elevated the cyber cat-and-mouse game to a completely new layer. In this layer, traditional firewalls are blind. The only countermeasure is deploying an AI-Native Defense Shield capable of detecting real-time traffic anomalies.
4. Global Reaction and the Splinternet

The introduction of Freedom.gov served as a deafening wake-up call for nations worldwide, including America's own allies. The concept we at Tekin Analysis have persistently championed as Sovereign Compute has now escalated from an academic theory to a matter of national survival.
4.1. Sovereign Compute as the Absolute Only Path to Survival
Nations have realized that as long as they are tethered to the global internet via foreign hardware, protocols, and software, they are completely defenseless against hegemonic platform attacks. If a country lacks domestic data centers, internal search engines, national social grids, and most importantly, independent processing silicon within its geographical borders, it is effectively a "digital colony." Ironically, the Freedom.gov project will violently accelerate the "Balkanization of the Internet" (The Splinternet); a future where the unified global web shatters into islands of isolated, nationalized, and hyper-defended networks.
The Final Verdict from Tekin Command Center
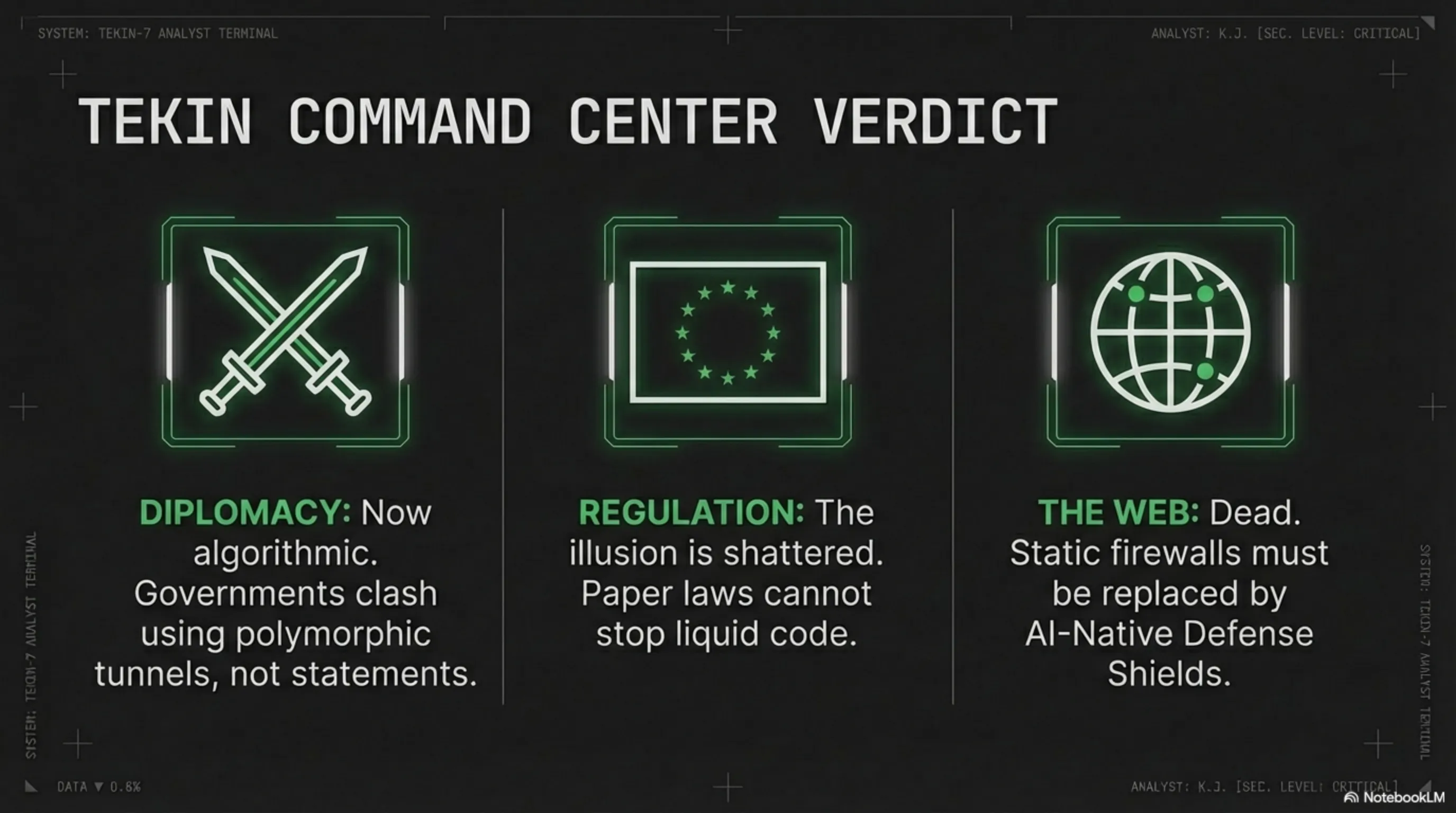
- ⚔️ The Birth of Algorithmic Diplomacy: Project Freedom.gov proved that governments no longer wage war through sanctions or political statements; they clash using code architecture, polymorphic tunnels, and network protocols.
- 🇪🇺 The Illusion of Regulation Shattered: The crisis between Washington and Brussels exposed that paper laws and bureaucracy (like the DSA) are incredibly fragile when pitted against the hardware power and software agility of Silicon Valley.
- 🌍 The Definitive Death of the Unified Web: The aggressive push to penetrate local networks forces governments to upgrade their static firewalls to smart defense shields, accelerating the rush toward independent, sovereign intranets.
Commander, autopsying this file revealed a bitter truth: in 2026, geographical borders only matter on paper maps. In reality, your border ends exactly where your code, protocols, and sovereign data centers end!
