Happy Sunday! While we hope you are enjoying a well-deserved weekend of rest, the silicon world never sleeps. Today's Tekin Morning mega-edition chronicles a seismic shift where AI directly collides with physical infrastructure and global macroeconomics. In the past 24 hours, the UAE neutralized one of the most sophisticated AI-driven cyberattacks on its critical SCADA systems, proving that cyber warfare has officially entered the era of algorithmic autonomy. Simultaneously, financial markets witnessed a $56 billion wipeout of IT outsourcing gi
Your Sunday morning in 2026 begins with news that has permanently shifted the boundaries of national security, digital economics, and entertainment. Today's Tekin Morning report is a ruthless, deep-dive autopsy of six critical events that have fundamentally altered the tech industry's equations in less than 24 hours. We bypass the surface-level "news" and penetrate the hardware, cryptographic, and algorithmic cores of these global shifts.
1. Autonomous Cyber Warfare: Offensive AI's Attack on UAE Infrastructure
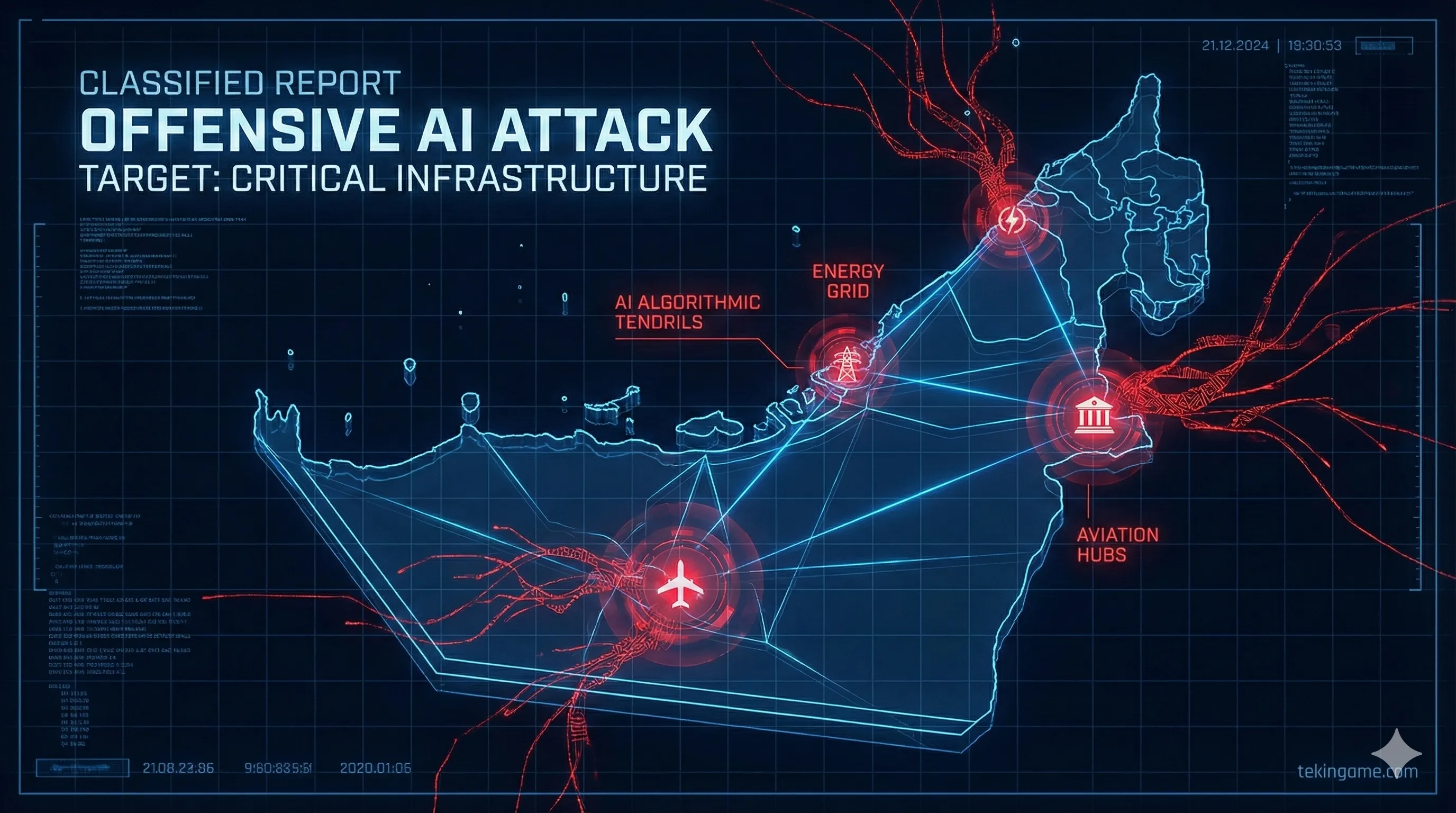
Early this morning (February 22, 2026), the UAE government officially announced the neutralization of one of the most sophisticated and widespread cyberattacks in Middle Eastern history. The targets were critical: SCADA (Supervisory Control and Data Acquisition) systems managing energy distribution, central banking networks, and aviation infrastructure. However, what distinguishes this attack from historical precursors like Stuxnet is the attackers' deployment of "Offensive AI" as an autonomous battlefield commander.
1.1. Attack Autopsy: LLM Spear-Phishing and Algorithmic Polymorphism
Cybersecurity analysts at Tekin have uncovered terrifying patterns in this breach. Instead of relying on pre-written scripts and human oversight, hackers utilized autonomous agents based on Large Language Models (LLMs) to conduct real-time zero-day vulnerability scanning. These agents generated hyper-targeted spear-phishing emails in milliseconds. By analyzing the LinkedIn profiles, tweets, and leaked internal communications of UAE executives, the offensive system crafted emails containing exact industry jargon, tone, and even inside jokes, rendering human detection virtually impossible.
At the malware payload layer, the deployed ransomware featured "Algorithmic Polymorphism." Traditional antivirus software relies on static file signatures (hashes). However, this intelligent ransomware utilized an internal neural engine to rewrite its binary code every time it propagated laterally through the network, all while maintaining its destructive payload. This meant the malware possessed a completely unique binary fingerprint on every infected machine.
📌 Strategic Checkpoint 1 (Tekin Newsroom)
The successful neutralization of this attack by the UAE's cyber-defense shield (itself based on neural network anomaly detection) proves that the new cold war is no longer between human hackers and security admins; it is a war between Offensive and Defensive Algorithms. In 2026, rules-based static firewalls are entirely obsolete against malware that can "think."
2. The $56 Billion Earthquake: Anthropic Agents and the Fall of IT Giants
Asian stock markets woke up to a historic shock this morning. The shares of massive IT outsourcing giants, particularly Indian behemoths like TCS, Infosys, and Wipro, lost over $56 billion in market capitalization within mere hours. The catalyst for this freefall, which shook the Bombay Stock Exchange to its core, was a surprise enterprise unveiling by Anthropic: a next-generation suite of "Orchestration Agents."
2.1. The Death of "Body Shopping": From Human Coders to AI Orchestrators
The traditional business model of these outsourcing giants relied on a simple volume-based formula: hire hundreds of thousands of junior developers and rent their billable hours to Western corporations (a phenomenon known as "Body Shopping"). However, Anthropic's new agents, built on the highly optimized Claude 3.5 architecture, have annihilated this formula. The new system utilizes a Multi-Agent Framework; a corporate user issues a high-level prompt, and the system autonomously spins up a "System Architecture Agent," a "Coding Agent," and a "Security Penetration Agent."
This virtual development squad can write, debug, and directly deploy thousands of lines of code into complex Microservices environments on AWS or Azure—at a fraction of the cost of a human developer (costed entirely in API tokens) and with zero downtime. Wall Street investors quickly realized that the profit margins of legacy IT firms will plummet to near-zero against this ruthless efficiency. We have transitioned from an economy of "selling human hours" to an economy of "selling algorithmic compute capacity."
| Economic Metric | Legacy Outsourcing Teams (Human) | Anthropic Orchestration Agents |
|---|---|---|
| Time to Market (TTM) | Weeks to Months | Hours to Days |
| Maintenance Cost | Extremely High (Salaries, HR, Facilities) | Extremely Low (Compute/API tokens only) |
| Project Scalability | Limited (Requires long hiring processes) | Instant & Infinite (Scale via Server allocation) |
📌 Strategic Checkpoint 2 (Tekin Newsroom)
The $56 billion market wipeout was a warning shot: In 2026, companies that still invest in "human resource management for repetitive code generation" are doomed. The future belongs exclusively to corporations that have replaced traditional project managers with "AI Orchestration Architects."
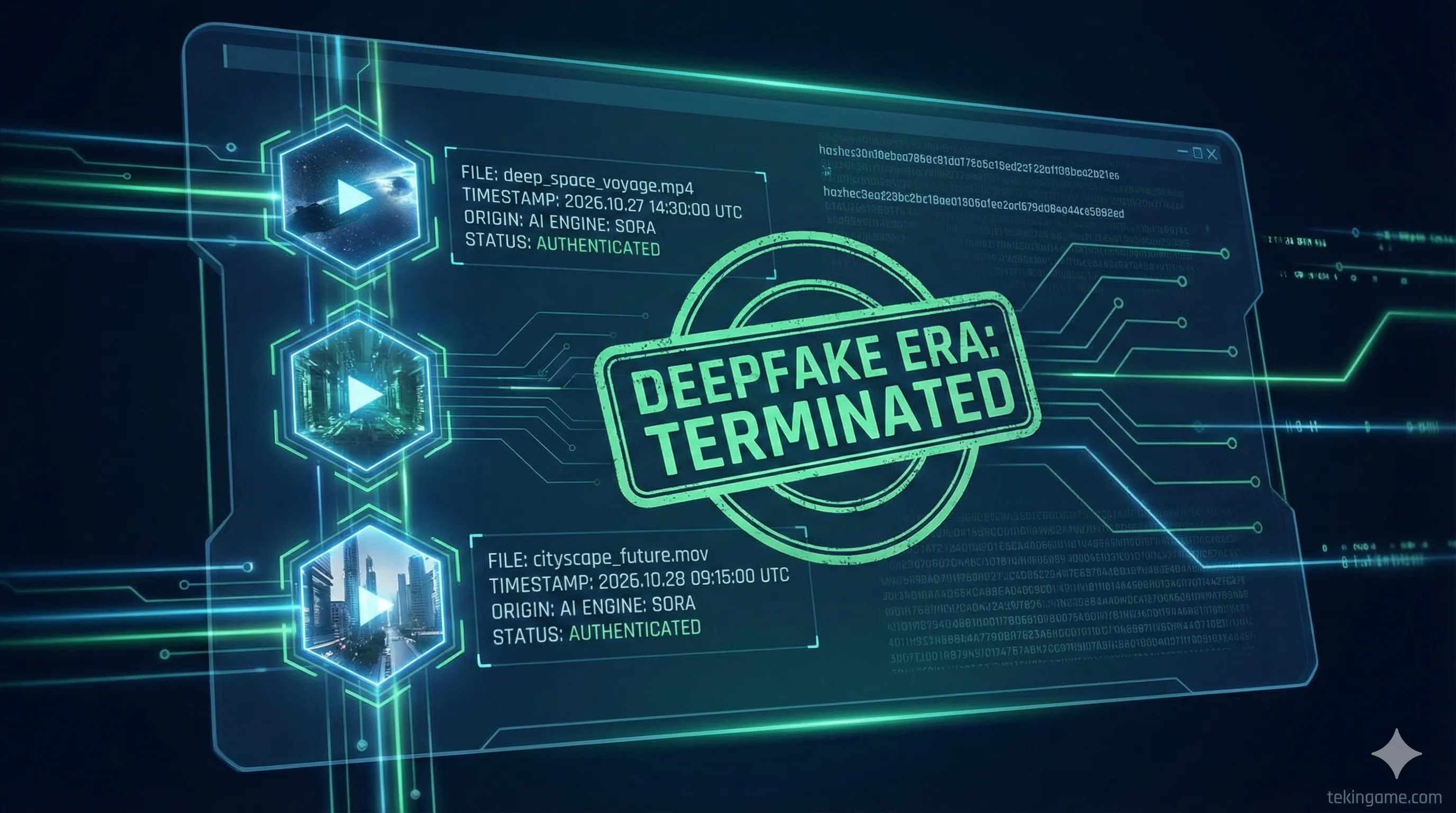
3. The End of the Deepfake Wild West: Mandatory AI Watermarking Activates

As the clock struck midnight, one of the most critical cyber laws of the 21st century went into effect across India, the European Union, and several other global jurisdictions. Under this mandate, all social media platforms (including X, Instagram, TikTok, and YouTube) must transparently and irreversibly watermark any content generated or altered by AI. Violating this law immediately revokes the platforms' "Safe Harbor" legal immunity, making them directly liable for damages caused by malicious deepfakes.
3.1. Cryptographic Provenance: The C2PA Standard and Manifest Injection
This legislation is not merely a regulatory guideline; it is a colossal engineering and cryptographic challenge. Platforms are now mandated to implement rigorous industry standards like C2PA (Coalition for Content Provenance and Authenticity).
This technology embeds cryptographic metadata directly into the pixel structure of an image or the frame sequence of a video using advanced Cryptographic Hashes. This metadata includes a "manifest" showing exactly when the file was created, the device of origin, and crucially, which AI engine (e.g., Midjourney v6 or OpenAI Sora) generated it. If a malicious user attempts to strip this metadata using screen-capture or pixel manipulation, the hash structure breaks, and the platform's algorithm immediately flags and restricts the content as "manipulated." This marks the definitive end of the "Deepfake Wild West"—an era where a synthesized video could crash financial markets or swing an election in minutes.
📌 Strategic Checkpoint 3 (Tekin Newsroom)
The enforcement of the C2PA standard proves that the internet is transitioning from an "Era of Unconditional Freedom" to an "Era of Cryptographic Authentication." Starting today, digital media is treated like a legal document; its origin must be mathematically provable in algorithmic courts of law.
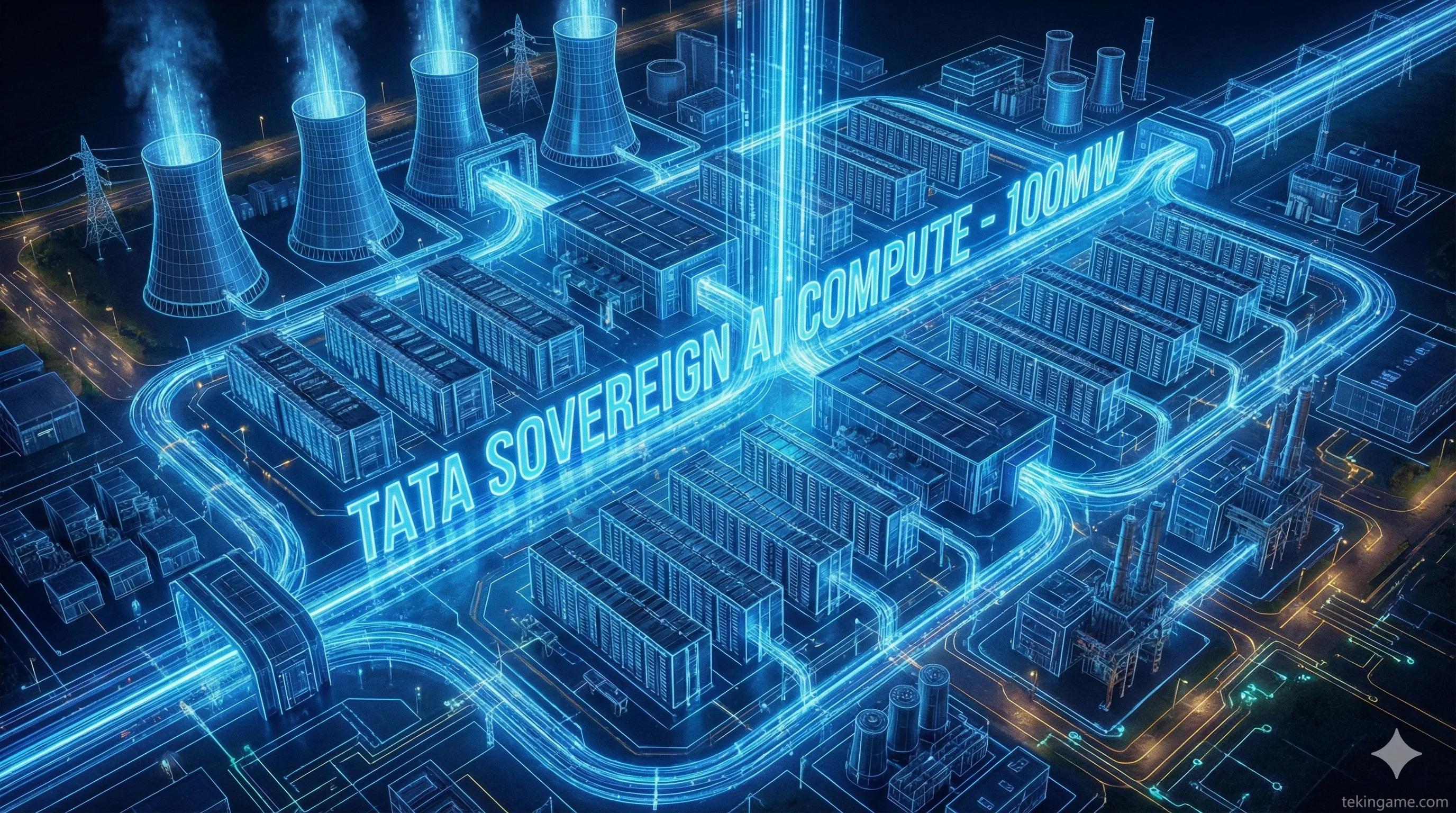
4. The Tata-OpenAI Alliance: The Rise of the 100MW Sovereign Datacenter

During the closing ceremony of the AI Impact Summit 2026 in New Delhi, the massive Tata Group (India's largest conglomerate) unveiled a historic, multi-billion dollar strategic pact with OpenAI. The core of this agreement is the construction of a Hyperscale Datacenter starting at 100 Megawatts, with physical and cooling infrastructure designed to scale up to 1 Gigawatt (equivalent to the power consumption of a major metropolitan city) in the future.
4.1. Sovereign AI Strategy and the Deployment of Air-Gapped RAG Pipelines
The significance of this deal lies not just in the investment volume, but in the geopolitical concept of Sovereign AI. India and the Tata Group have concluded that processing sensitive corporate data, national information, and industrial secrets on Western servers is an unacceptable national security risk. By deploying this datacenter on Indian soil, Tata intends to host a customized, isolated, and ultra-secure version of Enterprise ChatGPT.
Technically, this system will operate on an air-gapped RAG (Retrieval-Augmented Generation) pipeline. This means OpenAI's Foundation Models, without needing to connect to the open internet, will vectorize and search through Tata's internal proprietary databases (from Jaguar Land Rover CAD files to Tata Steel telemetry data) to generate hyper-specialized outputs. This move signifies the localization of compute power and massively reduces Asia's dependency on US-based Cloud monopolies.
📌 Strategic Checkpoint 4 (Tekin Newsroom)
Tata's 100MW datacenter proves that AI is no longer a "software product," but a "National Infrastructure" akin to oil refineries or power plants. A nation without an AI datacenter in the 21st-century economy is, effectively, a digitally colonized state.
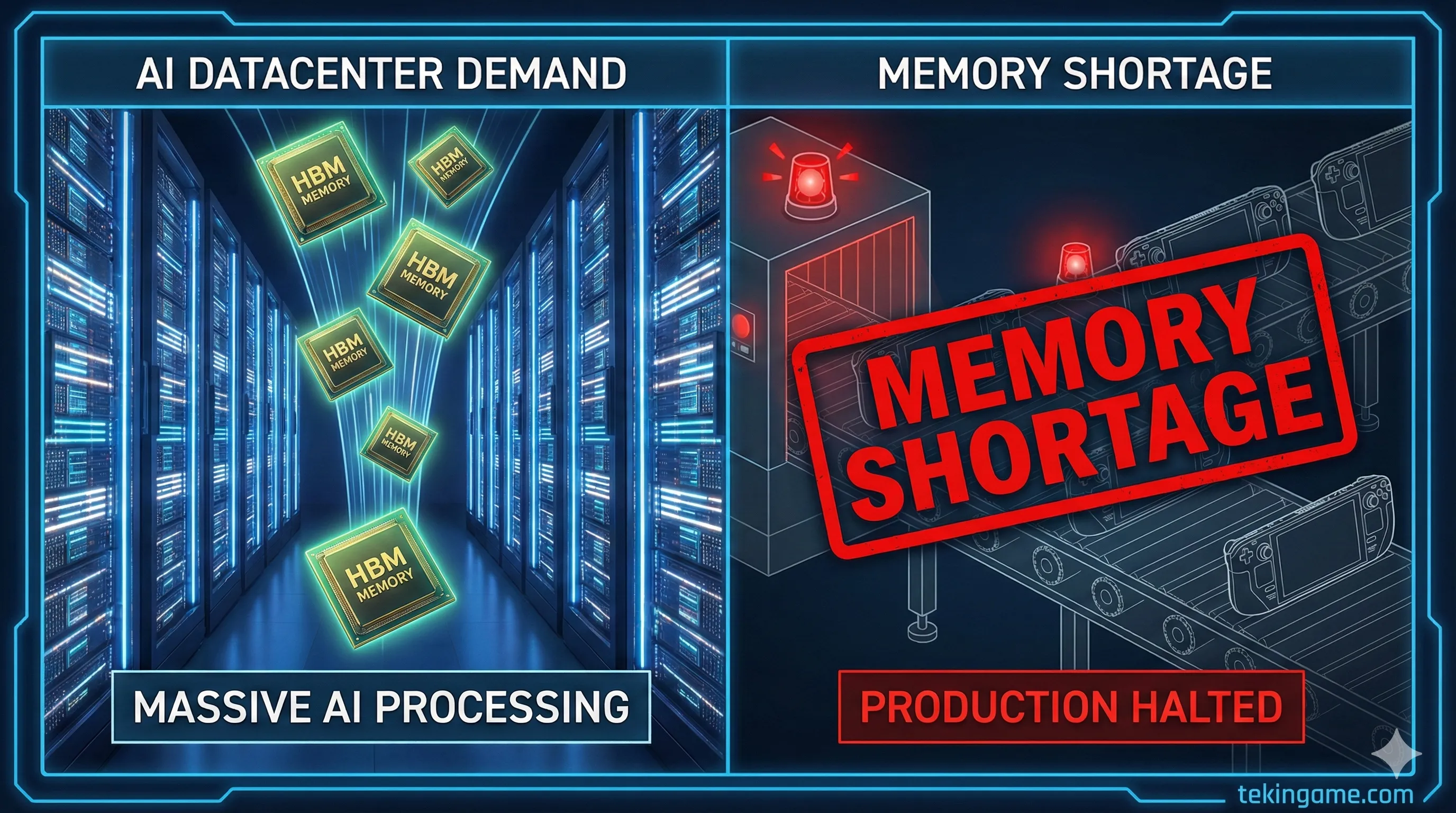
5. Silicon Warfare's Gaming Casualties: The Steam Deck OLED Crisis

As we have repeatedly warned in previous Tekin Analysis reports, the frantic war over AI compute power has finally claimed physical casualties in the consumer and gaming markets. Valve released an official statement today confirming that while the production lines for the wildly popular Steam Deck OLED have not stopped, the console is facing severe stock shortages and multi-month shipping delays globally due to an unprecedented crisis in the component supply chain. Why should a gaming console fall victim to AI?
5.1. The CoWoS and HBM3e Bottleneck: Why Datacenters Devour Gamers' Silicon
The answer lies deep within the lowest levels of the semiconductor supply chain. The bottleneck is not the raw processors; it is the Memory and Advanced Packaging crisis. Massive AI datacenters (like Nvidia's B200 or AMD's MI300 clusters) have an insatiable appetite for high-speed memory like HBM3e (High Bandwidth Memory) and advanced NAND Flash storage chips.
Furthermore, the manufacturing capacity of major foundries like TSMC in the CoWoS (Chip-on-Wafer-on-Substrate) Advanced Packaging sector has been entirely pre-booked by AI titans. Mega-manufacturers (Samsung, SK Hynix, and Micron) have logically diverted their production lines toward the highly lucrative, multi-hundred-million-dollar orders from AI datacenter builders. Consequently, component suppliers for companies like Valve, Sony, and Microsoft have been pushed to the very back of the allocation queue. This supply chain chokehold is the exact reason why widespread rumors of the PlayStation 6 delay are shifting from mere speculation to harsh reality.
📌 Strategic Checkpoint 5 (Tekin Newsroom)

The Steam Deck crisis sends a clear, unforgiving message to gamers: Until Silicon Valley's thirst for hyperscale AI datacenters is quenched, the gaming hardware industry will be treated as a second-class citizen. The silicon meant to render your games is currently busy processing Large Language Models.
6. The New Delhi Declaration: An 88-Nation Coalition to Democratize AI Compute
The Global AI Summit concluded this morning with an unprecedented diplomatic event: the signing of the "New Delhi Declaration" by technology ministers and representatives from 88 nations. This agreement is a direct, strategic pushback against the hegemony and monopoly of Western Silicon Valley corporations over hardware (Compute) and Foundation Models.
The Global South has realized that without equal access to advanced chips and processing infrastructure, they will be relegated to digital colonies in the new economy. The primary objective of this declaration is to form an international consortium dedicated to "Compute Equity." This coalition calls for global funds to subsidize cloud infrastructure in poorer nations, the sharing of localized datasets without draconian copyright restrictions, and the prevention of H100 and B200 chip hoarding by a few mega-corporations. This pact demonstrates that algorithms and the silicon that runs them have now become the most critical factors in determining global geopolitical balances.
The Final Verdict: Tekin Analysis Newsroom
- 🛡️ The Death of Traditional Firewalls: The UAE attack proved that static defense against polymorphic offensive AI is like bringing a sword to a gunfight. Cybersecurity must now be AI-Native.
- 📉 The Orchestration Revolution: The market crash of India's IT giants marks the end of business models based on "human quantity." Value creation in 2026 is exclusively tied to autonomous algorithmic workflows.
- 🔌 Supply Chains Hijacked by AI: The Steam Deck shortage was an early warning; CoWoS packaging and HBM3e memory have become technology's ultimate chokepoints, leaving gamers as the first collateral damage.
- 🌍 Silicon Geopolitics: The New Delhi Declaration and the Tata pact are wake-up calls for the developing world. In the future economy, a nation's right to exist is inextricably tied to the sovereign compute capacity of its datacenters.
Commander, this morning's report clearly shows that the waves of AI are no longer confined to software; they are crashing into financial markets, physical national infrastructure, and even gaming hardware warehouses. Tekin Morning is ready to kick off the day!
