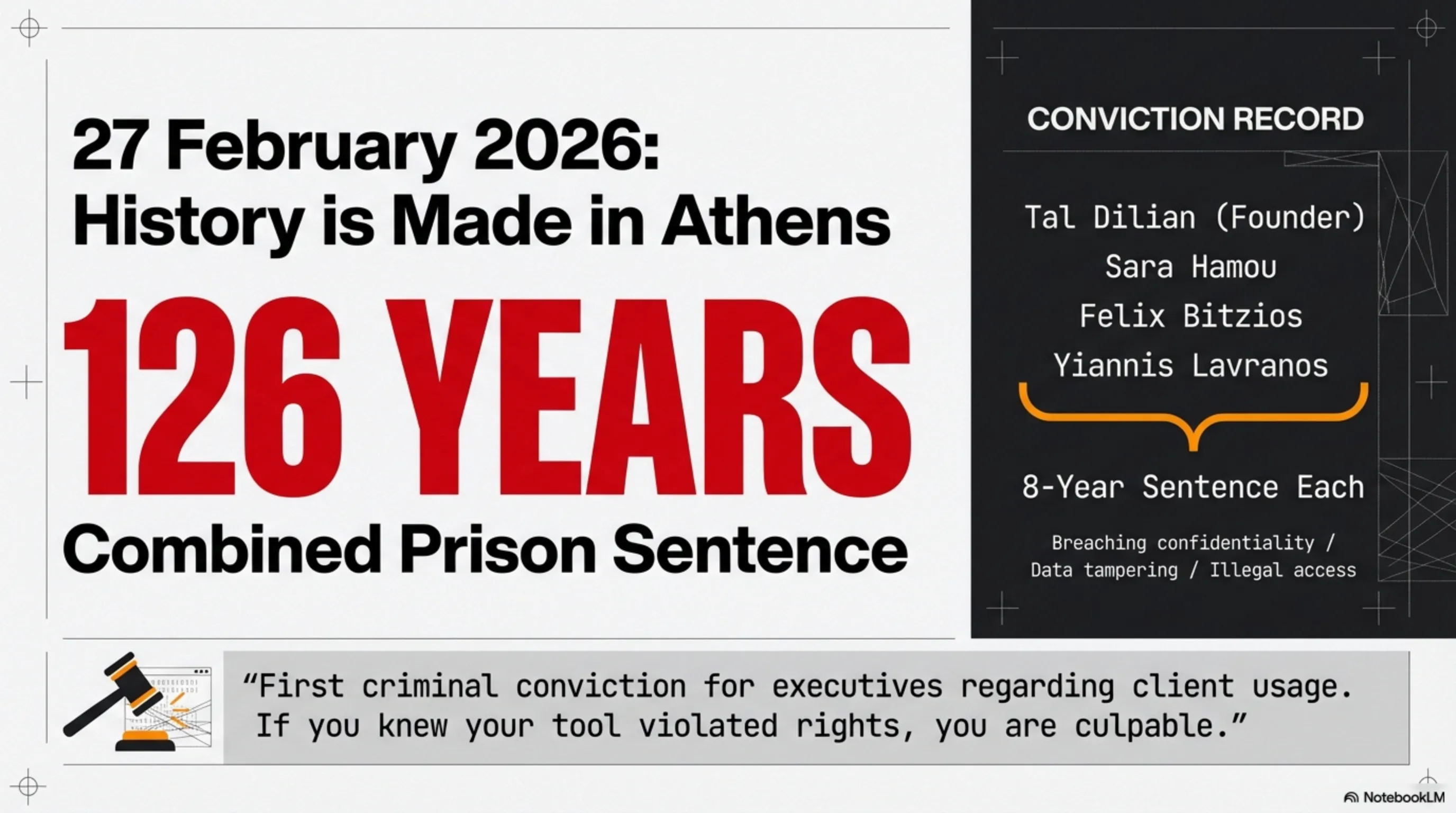
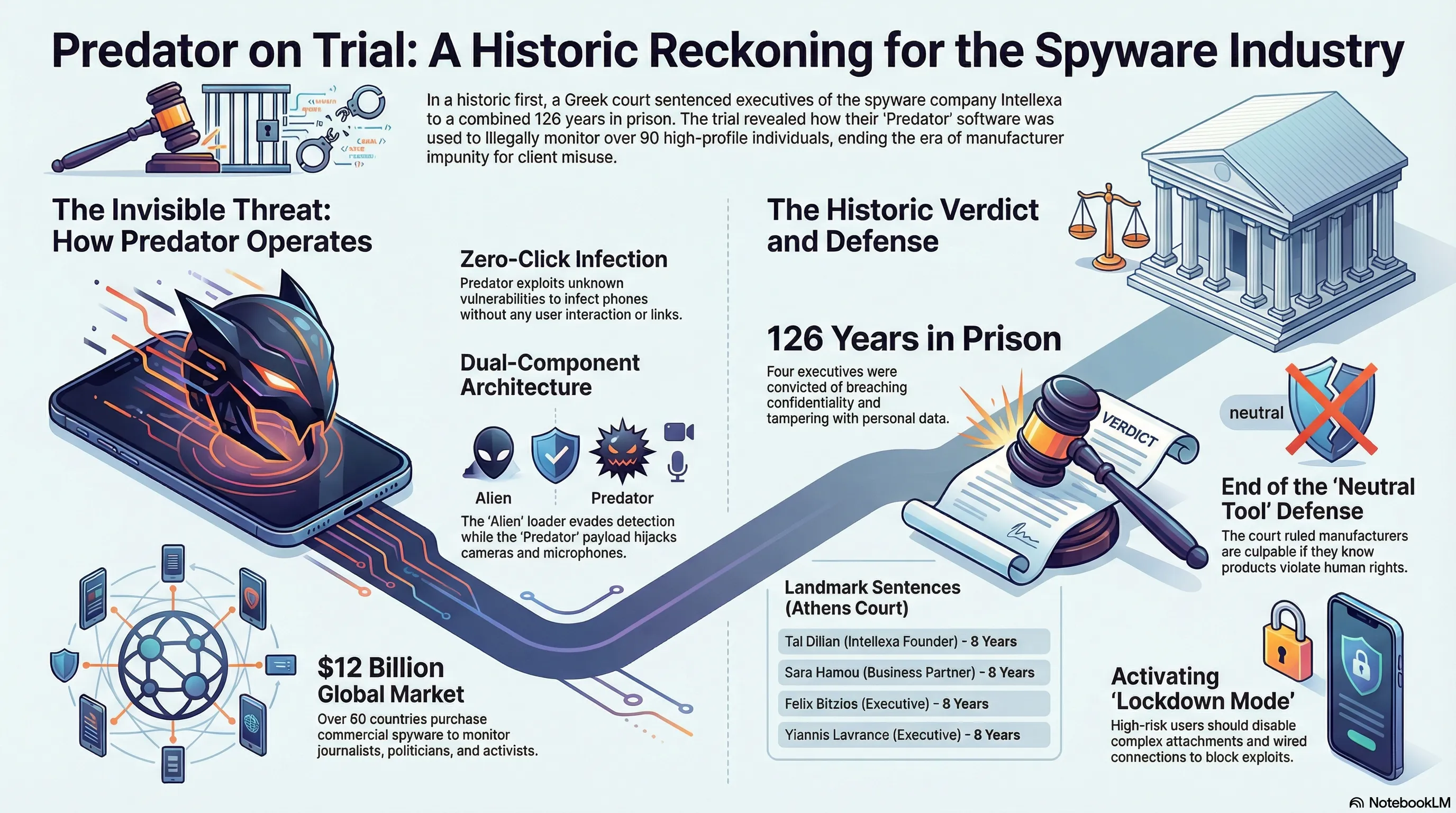
On 27 February 2026, a Greek court issued a historic verdict that could transform the future of the commercial spyware industry: Tal Dilian, founder of Intellexa and creator of the Predator spyware, along with three others, were sentenced to a combined 126 years and 8 months in prison. This is the first criminal conviction in history for executives of a commercial spyware company - not for building the tool, but for how their clients used it. The Predatorgate scandal began in early 2022 when Thanasis Koukakis, a Greek investigative journalist, discovered his phone had been simultaneously targeted by the Greek National Intelligence Service (EYP) and Predator spyware. Subsequent investigations revealed that more than 90 individuals - including Nikos Androulakis, leader of the opposition PASOK party, government ministers, military officials, prosecutors, and journalists - were victims of this spyware. Predator is sophisticated spyware that can infect iOS and Android phones without any victim interaction (Zero-Click Exploit). This means you need not click on a suspicious link; it suffices for your phone to be switched on. Predator exploits Zero-Day vulnerabilities and can be activated through iMessage, WhatsApp, or even online advertisements. Once installed, Predator has complete access to the phone: call recording, reading encrypted messages (Signal, WhatsApp, Telegram), camera and microphone access, GPS location tracking, and reading emails and photos. This tool can transform your phone into a 24-hour listening device without your knowledge. The Athens court convicted four individuals on three principal charges: breaching confidentiality of telephone communications, tampering with personal data filing systems, and illegal access to information systems. Judge Nikos Askianakis stated that the defendants acted with joint intent and no mitigating circumstances existed. All four remain free pending appeal. Intellexa sold spyware to some of the world's worst human rights violators: Sudan's Rapid Support Forces whose actions bear hallmarks of genocide, Egyptian intelligence services, the Vietnamese government which attempted to hack American officials, and the governments of Angola and Pakistan. Even after US sanctions in March 2024, Intellexa remained active in May 2024, targeting Angolan journalist Teixeira Cândido. This verdict occurs in the context of a larger crisis: the European Parliament launched the PEGA committee in 2022, which revealed that Spain, Hungary, and Poland all used commercial spyware against their own citizens. The committee recommended that spyware use should be prohibited, but implementation has been slow. To protect themselves, high-risk users (journalists, activists, politicians) should use Apple's Lockdown Mode, keep their phones updated, use two separate phones, and monitor unusual phone behaviour (rapid battery drain, heating). Services like Amnesty International's Mobile Verification Toolkit can scan phones for spyware. The future vision presents three scenarios: end of the impunity era (probability 40%), migration of companies to safe jurisdictions (probability 45%), or nationalisation of the industry (probability 15%). The more probable scenario is that spyware companies will relocate to countries with lenient laws and remain active. This verdict establishes an important legal precedent: surveillance tool manufacturers cannot hide behind their government clients. If you knew your product was being used to violate rights, you are also responsible. But the question is: will this verdict stand, or will it be overturned on appeal? And will other courts follow this precedent?
Introduction: The Day the Spyware Industry Was Put on Trial
Greetings, Tekin Army! Imagine your phone is listening to you. The camera is active, the microphone is on, and all your messages - even those encrypted in Signal or WhatsApp - are being read. And you notice nothing. This is no longer a spy film scenario; this is the reality of Predator - spyware that targeted 90 Greek politicians, journalists, and military officials.
On 27 February 2026, a Greek court issued a historic verdict: Tal Dilian, founder of Intellexa and creator of Predator, along with three others, were sentenced to a combined 126 years and 8 months in prison. This is the first criminal conviction in history for executives of a commercial spyware company - not for building the tool, but for how their clients used it.
This is an inflection point. For years, the commercial spyware industry operated with complete impunity. Companies like NSO Group (maker of Pegasus) and Intellexa would say: "We merely build tools; responsibility for use lies with the client." But the Athens court rejected this defence and declared: if you knew your tool was being used to violate human rights, you are also culpable.
Technical Autopsy: How Does Predator Work?
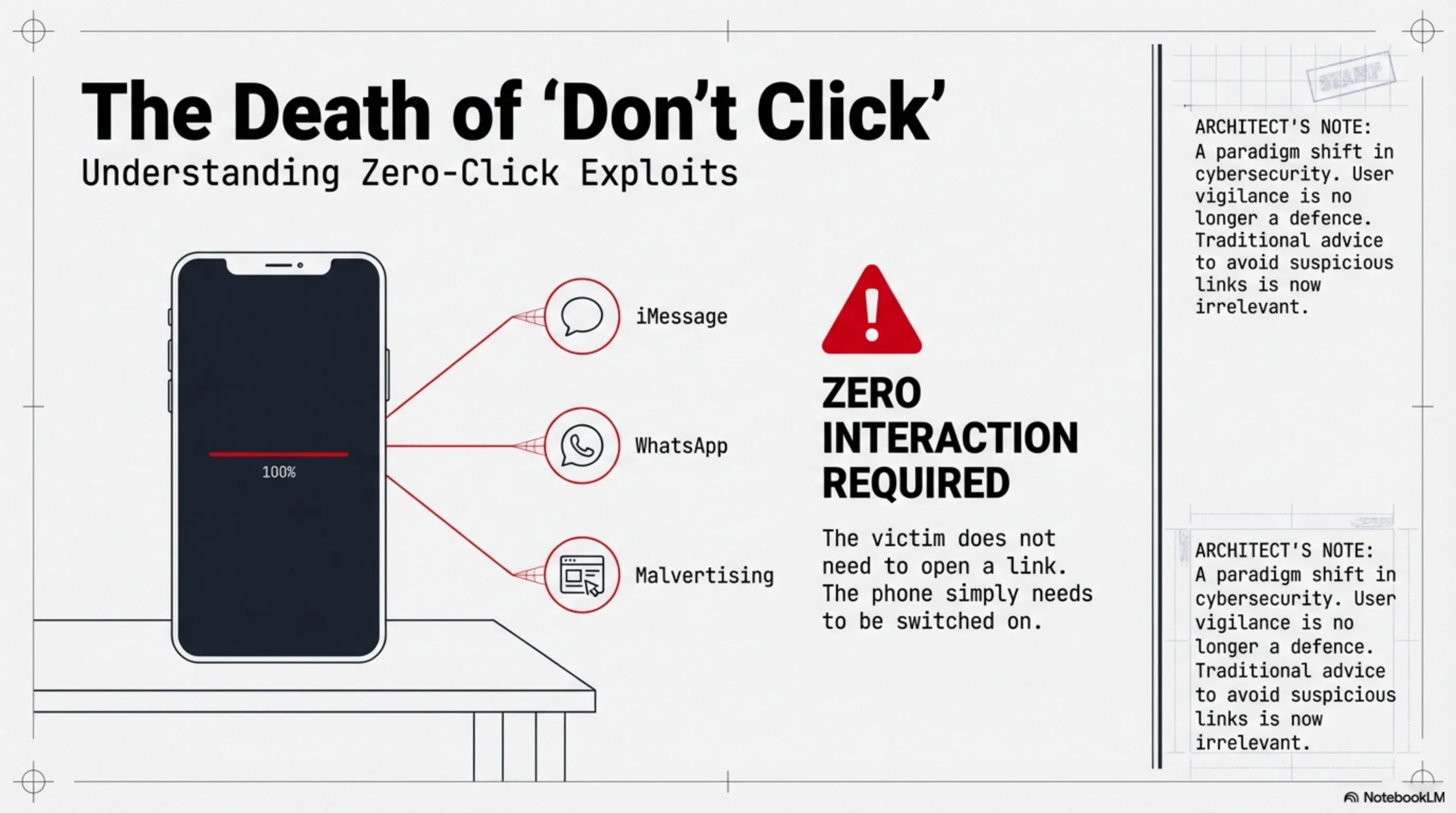
Zero-Click Exploits: Attack Without a Click
Predator is sophisticated spyware that can infect iOS and Android phones without any interaction from the victim. This means you need not click on a suspicious link or download a file; it suffices for your phone to be switched on.
How? Predator exploits Zero-Day vulnerabilities - bugs in the operating system that have not yet been discovered. These vulnerabilities can be activated through iMessage, WhatsApp, or even online advertisements (Malvertising).
Architect's Note: Zero-Click exploits represent a paradigm shift in cybersecurity. Previously, we told users: "Don't click suspicious links." But now clicking is irrelevant; merely having a phone switched on suffices.
Predator Architecture: Alien + Predator
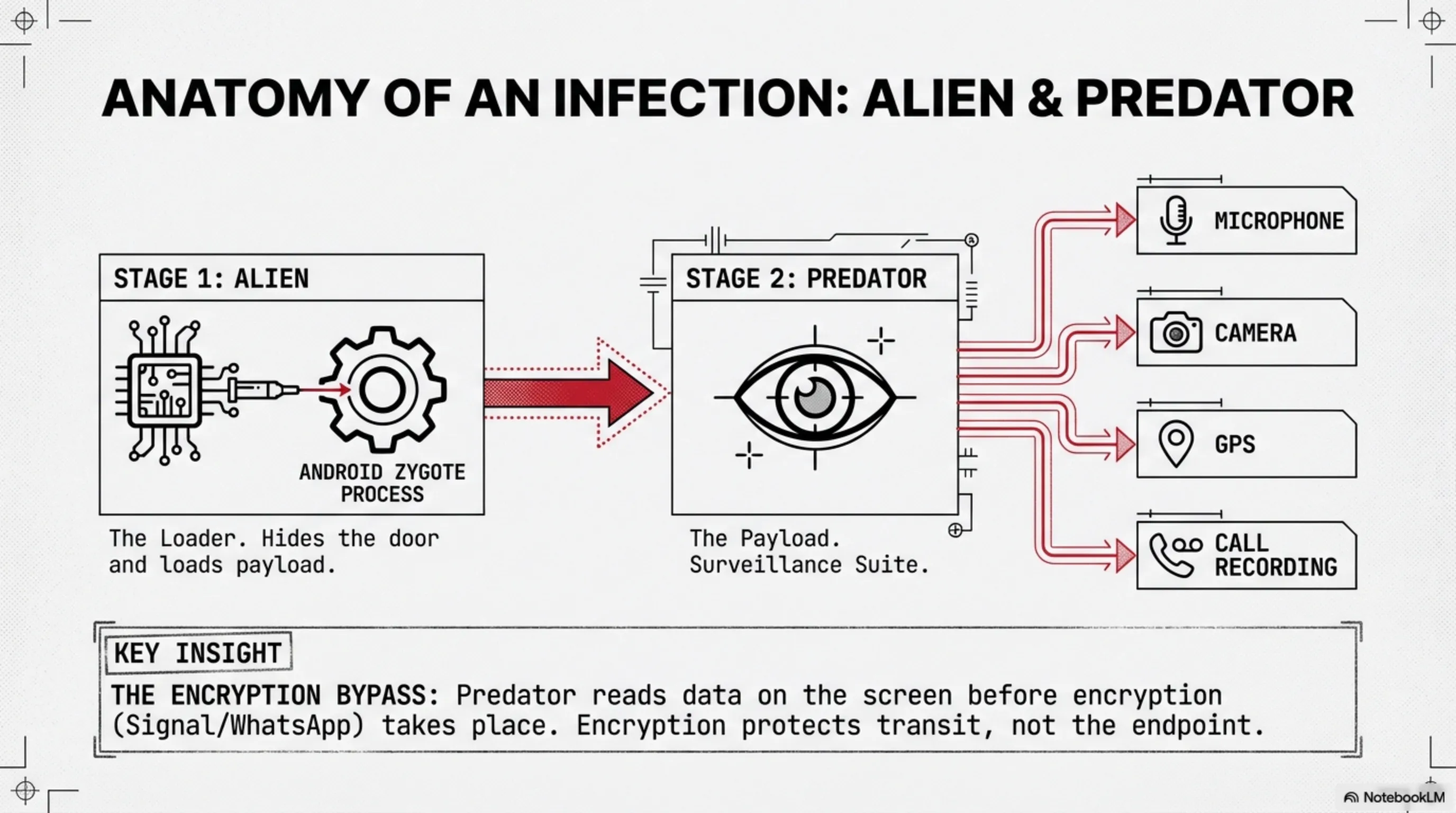
Predator comprises two primary components:
- Alien (Loader): This is the first component installed on the phone. Its function is to load and execute other modules. Alien injects itself into a core Android process called Zygote to evade detection.
- Predator (Payload): This is the main component with all surveillance capabilities: call recording, message reading, camera and microphone access, and GPS location tracking.
Predator can steal data from all encrypted messaging apps like Signal, WhatsApp, and Telegram. How? Because encryption only works during transmission; when a message is displayed on your phone, it is no longer encrypted. Predator reads it at that moment.
The Predatorgate Scandal: Who Was Targeted?
90+ Victims: From Politicians to Journalists
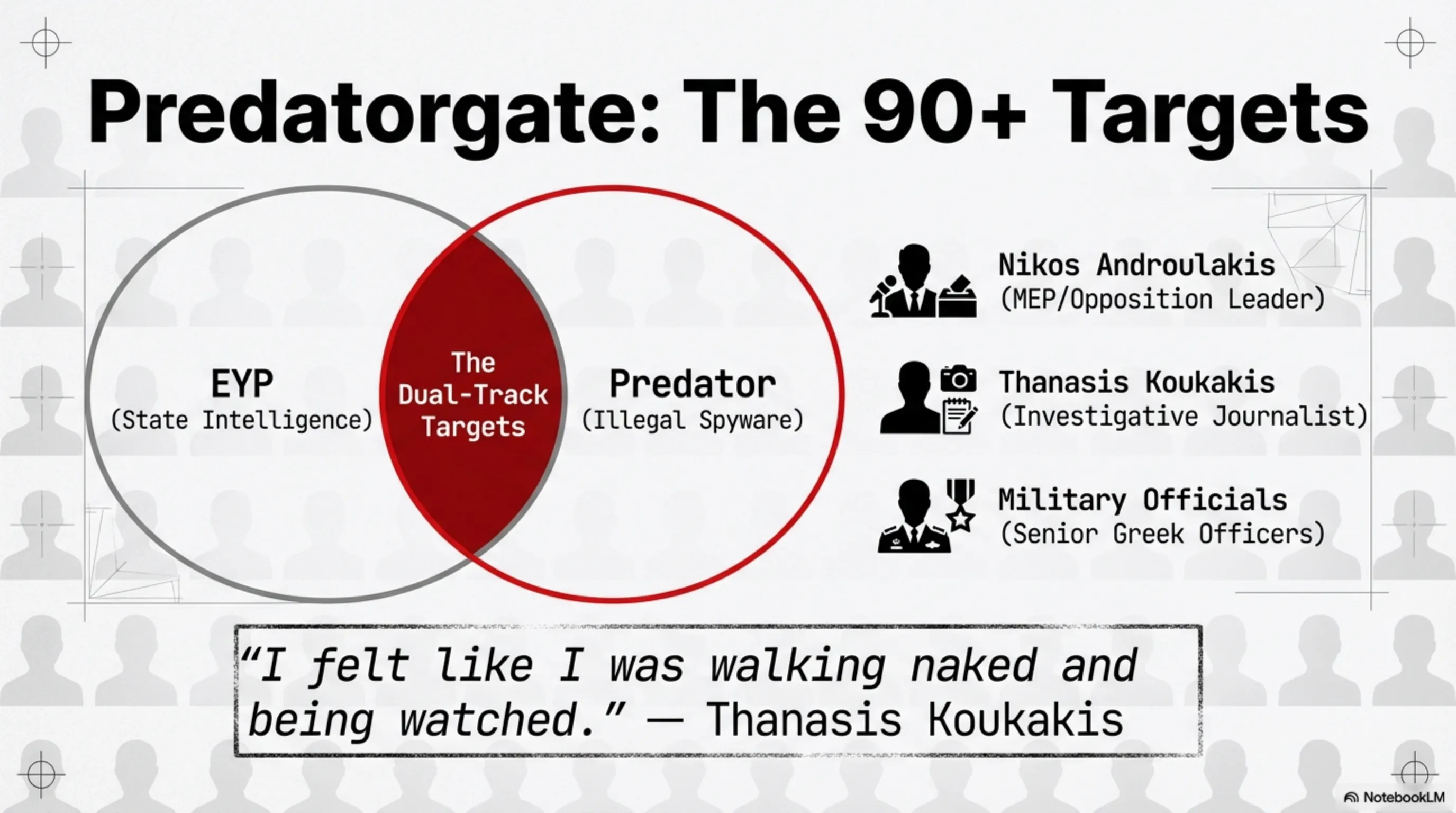
Investigations revealed that Predator was used against more than 90 individuals in Greece. Victims included:
- Nikos Androulakis: Leader of opposition party PASOK and Member of European Parliament
- Thanasis Koukakis: Investigative journalist reporting on corruption in Greece's banking sector
- Government ministers: Even some ministers of the current Greek government were targeted
- Military officials: Senior officers of the Greek military
- Prosecutors and lawyers: Those investigating corruption
But the terrifying aspect is this: many of these victims were under dual-track surveillance. That is, both the Greek National Intelligence Service (EYP) was legally monitoring them, and Predator was illegally spying on them. This suggests there was likely coordination between the government and spyware manufacturers.
Thanasis Koukakis: The Journalist Who Exposed It All
The story began in early 2022. Thanasis Koukakis, an investigative journalist, noticed his phone behaving strangely: battery draining rapidly, phone heating up, and excessive data consumption. He sent his phone to Citizen Lab - a security laboratory at the University of Toronto.
The result was shocking: his phone had been simultaneously targeted by EYP (Greek intelligence service) and Predator. This was the first time a victim of commercial spyware in Europe was publicly identified. Koukakis went to court and filed a case against the Greek government and Intellexa.
He stated in an interview: "I felt like I was walking naked and being watched. I didn't know what content had been stolen from my phone, what emails had been read, and what conversations had been monitored."
Geopolitical Analysis: The Commercial Spyware Industry
From Pegasus to Predator: A Billion-Dollar Surveillance Market
Intellexa is not the sole player in this industry. Israeli NSO Group with Pegasus, Italian Hacking Team, and German FinFisher are all active in this market. What is the value of this market? Estimates range from $5 to $12 billion annually.
Why is this market so lucrative? Because more than 80 countries globally are clients of these companies. From Western democracies like Spain and Poland to repressive regimes like Saudi Arabia, Egypt, and Sudan.
This article continues our analysis of the Hardware Rebellion and AI Paradox - where we saw how technology can turn against its creators and users. But Predatorgate is a level higher: technology deliberately built to violate human rights.
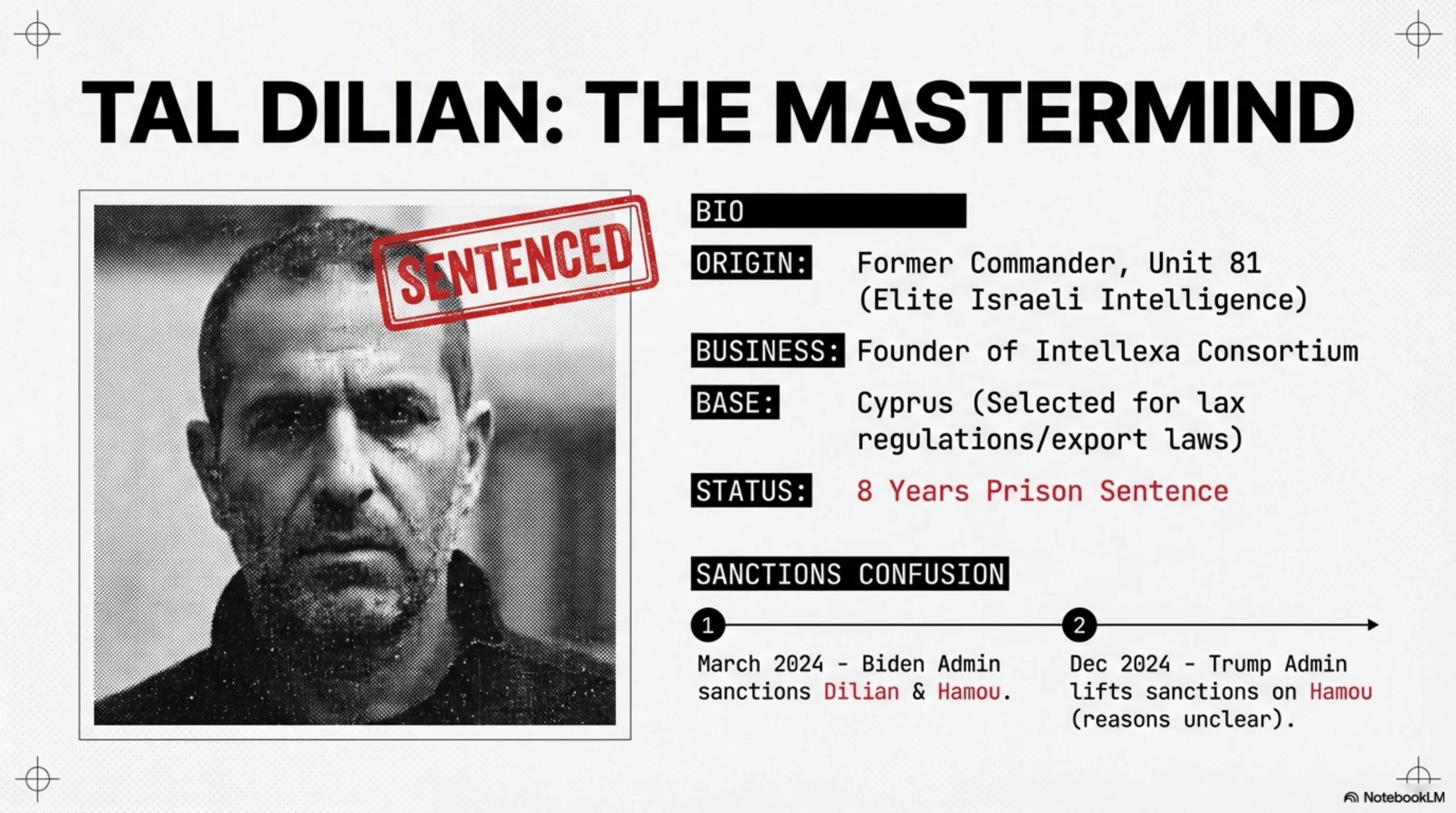
Tal Dilian: From Israeli Intelligence Officer to Greek Prisoner
Tal Dilian is a former Israeli military intelligence officer who worked in an elite unit. After leaving the military, he founded Intellexa - a consortium of spyware companies whose flagship product was Predator.
Intellexa used Cyprus as its operational base. Why Cyprus? Because its tax and regulatory laws are extremely lenient. Spyware companies can register in Cyprus and easily provide services to clients worldwide.
In March 2024, the Biden administration imposed sanctions on Dilian, Sara Hamou (his ex-wife and business partner), and several Intellexa-affiliated companies. But in December 2024, the Trump administration lifted sanctions on Hamou - a controversial decision whose reasons remain unclear.
The Court Verdict: Why Is This Historic?
Charges and Sentences
The Athens court convicted four individuals on three principal charges:
- Breaching confidentiality of telephone communications: Illegal wiretapping of calls and messages
- Tampering with personal data filing systems: Accessing and altering private information
- Illegal access to information systems: Hacking devices without authorisation
Sentences:
- Tal Dilian: 8 years in prison
- Sara Hamou: 8 years in prison
- Felix Bitzios: 8 years in prison
- Yiannis Lavranos: 8 years in prison
Judge Nikos Askianakis stated that the defendants acted with "joint intent" and no mitigating circumstances existed. All four remain free pending appeal, which their lawyers have requested within the statutory 10-day window.
Architect's Analysis: This verdict establishes an important legal precedent: surveillance tool manufacturers cannot hide behind their government clients. If you knew your product was being used to violate rights, you are also responsible.
Intellexa's Clients: From Greece to Sudan
The Blacklist: Who Purchased Predator?
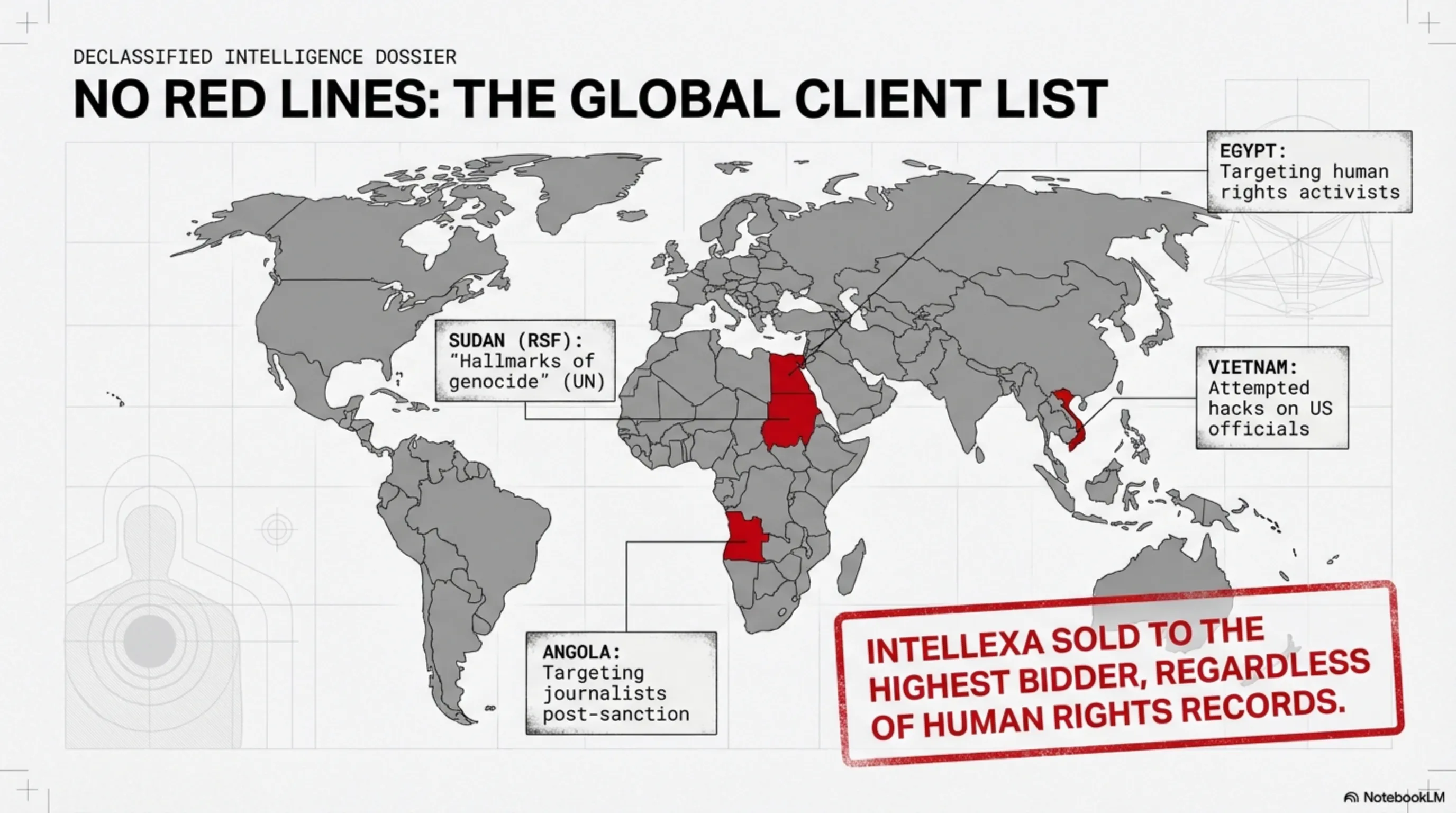
Investigations have shown that Intellexa sold spyware to some of the world's worst human rights violators:
- Sudan: Rapid Support Forces (RSF) whose actions have been described by UN experts as bearing "hallmarks of genocide"
- Egypt: Intelligence services that used Predator against human rights activists
- Vietnam: A government that attempted to hack American officials
- Angola: In May 2024, prominent journalist Teixeira Cândido was targeted with Predator
- Pakistan: In summer 2025, a human rights lawyer was targeted
This list demonstrates that Intellexa had no red lines. They sold spyware to anyone who paid - regardless of how it would be used.
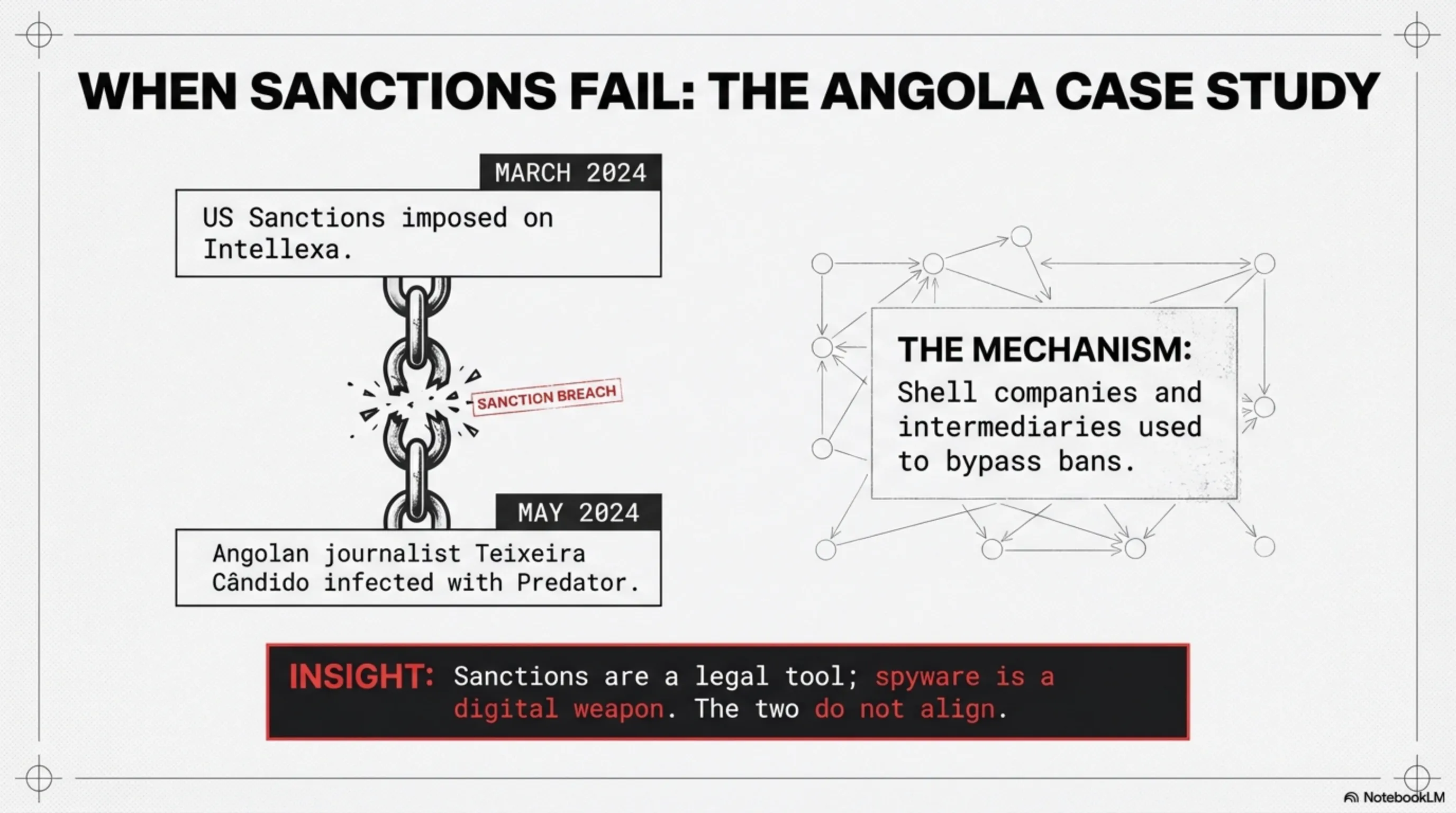
The Angola Case: When Sanctions Don't Work
One of the most concerning aspects of this case is that even after US sanctions in March 2024, Intellexa remained active. In May 2024 - two months after sanctions - Teixeira Cândido's phone, an Angolan journalist, was infected with Predator.
Cândido told ICIJ: "I was scared, of course, because I didn't know what content they took from my phone, from my emails, and I didn't know what they had listened to. It feels like you're walking naked and being watched."
This demonstrates that sanctions alone are insufficient. Intellexa uses a complex network of shell companies and intermediaries to evade sanctions. This is a major challenge for governments.
Risks and Challenges: Why This Is Just the Beginning
The Spyware Industry Remains Alive
Despite this historic conviction, the commercial spyware industry continues to grow. Why? Because demand exists. Governments want the capability to spy on their citizens, and private companies are willing to sell that capability.
NSO Group, maker of Pegasus, remains active. Despite numerous lawsuits in America and international sanctions, the company continues serving its clients. Why? Because the Israeli government supports it and authorises its exports.
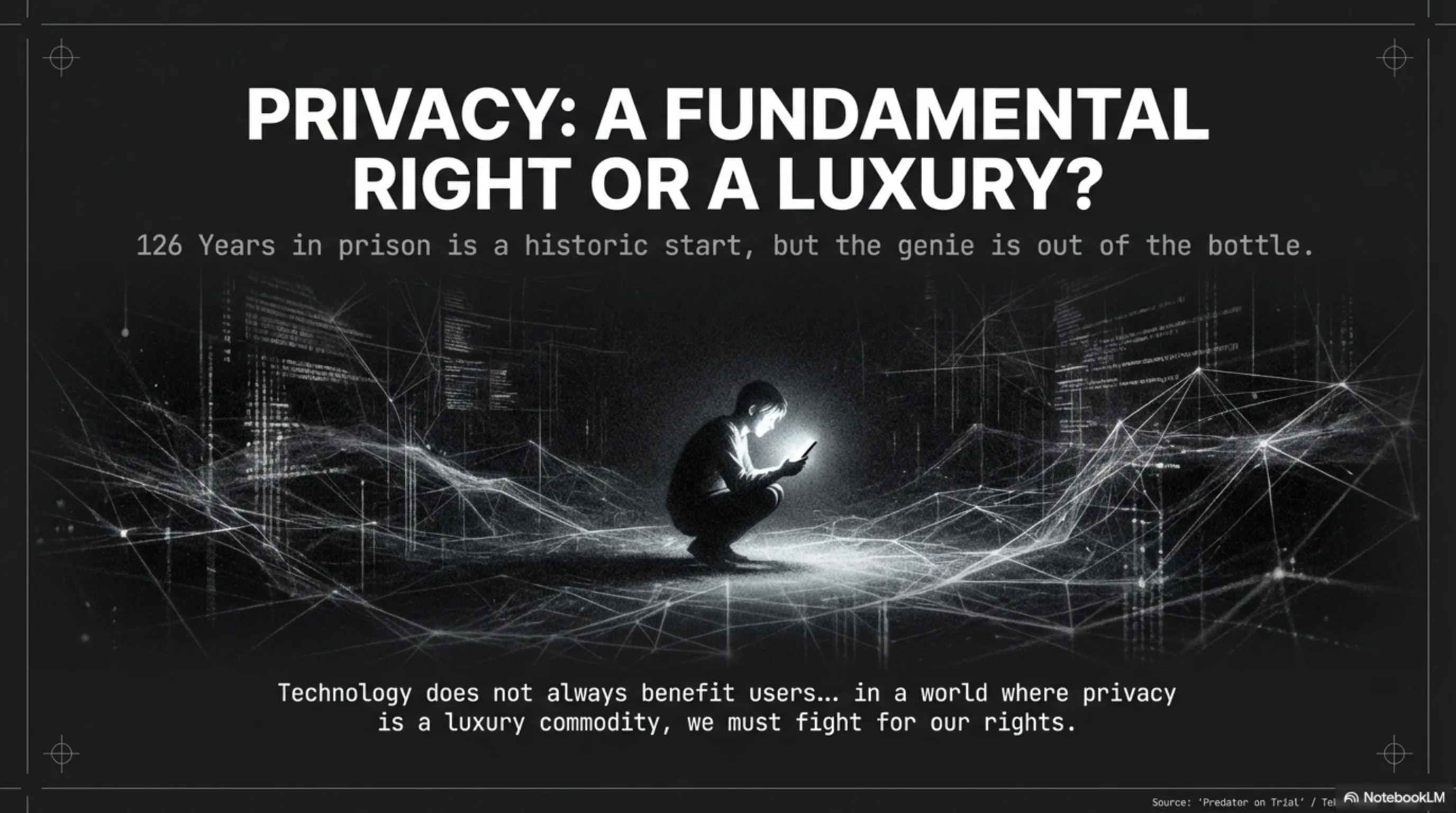
Architect's Warning: We are entering a world where privacy is a luxury commodity, not a fundamental right. If you are a politician, journalist, or activist, you must assume your phone is being monitored.
Comparison with the Arms Industry: Should Spyware Be Regulated?
Some experts have suggested that spyware should be regulated like weapons. That is, its sale to certain countries should be prohibited, and buyers must obtain licences. But the problem is that spyware is a digital product; it cannot be controlled like a tank or missile.
Moreover, many Western countries themselves use commercial spyware. Spain used Pegasus against Catalan leaders. Poland used it against political opponents. Germany and France have also been NSO Group clients. So how can they demand others not use it?

Technical Solutions: How to Protect Yourself
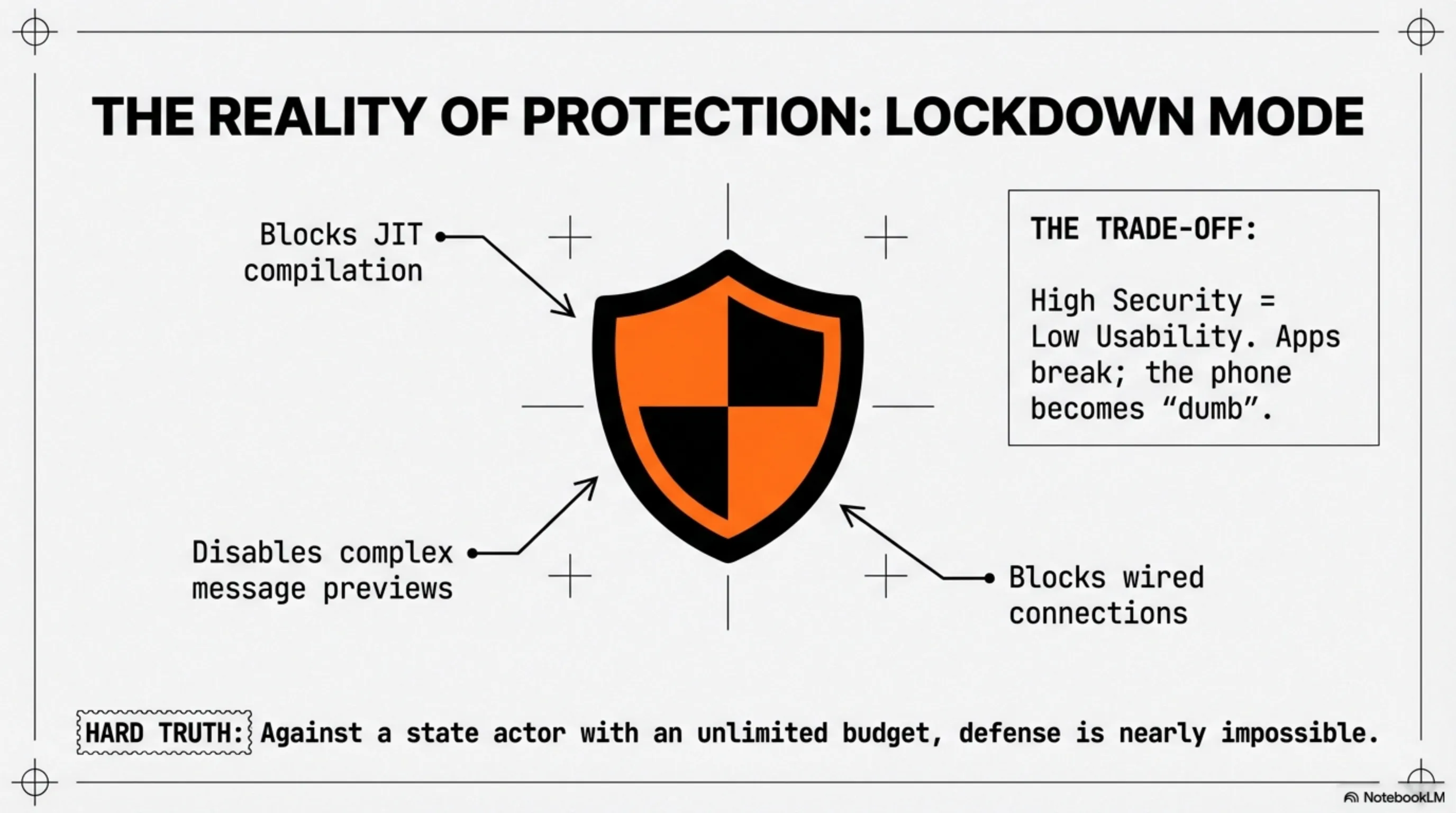
Lockdown Mode: Apple's Shield Against Spyware
In 2022, Apple introduced a new feature called Lockdown Mode. This mode disables many phone capabilities to prevent Zero-Click exploits. For instance:
- Complex attachments in iMessage are disabled
- Link previews in messages are disabled
- Wired connections (USB) are disabled when the phone is locked
- Some complex web technologies (like JIT compilation) are disabled
This feature is very useful for high-risk individuals (journalists, activists, politicians). But the problem is that using it causes some applications to malfunction.
In our recent article about Gemini 3.1 Pro and the Agentic AI Revolution, we saw that OpenAI has also introduced a Lockdown Mode. This shows that security is becoming a core priority in the technology industry.
Practical Recommendations for High-Risk Users
If you are a journalist, activist, or politician, take these recommendations seriously:
- Use Lockdown Mode: Even if it is inconvenient
- Keep your phone updated: Security updates are critical
- Use two phones: One for sensitive work, one for daily use
- Monitor your phone's behaviour: Battery draining rapidly? Phone heating up? Excessive data consumption?
- Test your phone: Services like Amnesty International's Mobile Verification Toolkit can scan your phone for spyware
But the bitter reality is: if a government with a budget of millions decides to target you, it will likely succeed. These tools are so sophisticated that even security experts struggle to detect them.
International Response: Europe Is Taking Action
The PEGA Committee: European Parliament Investigation
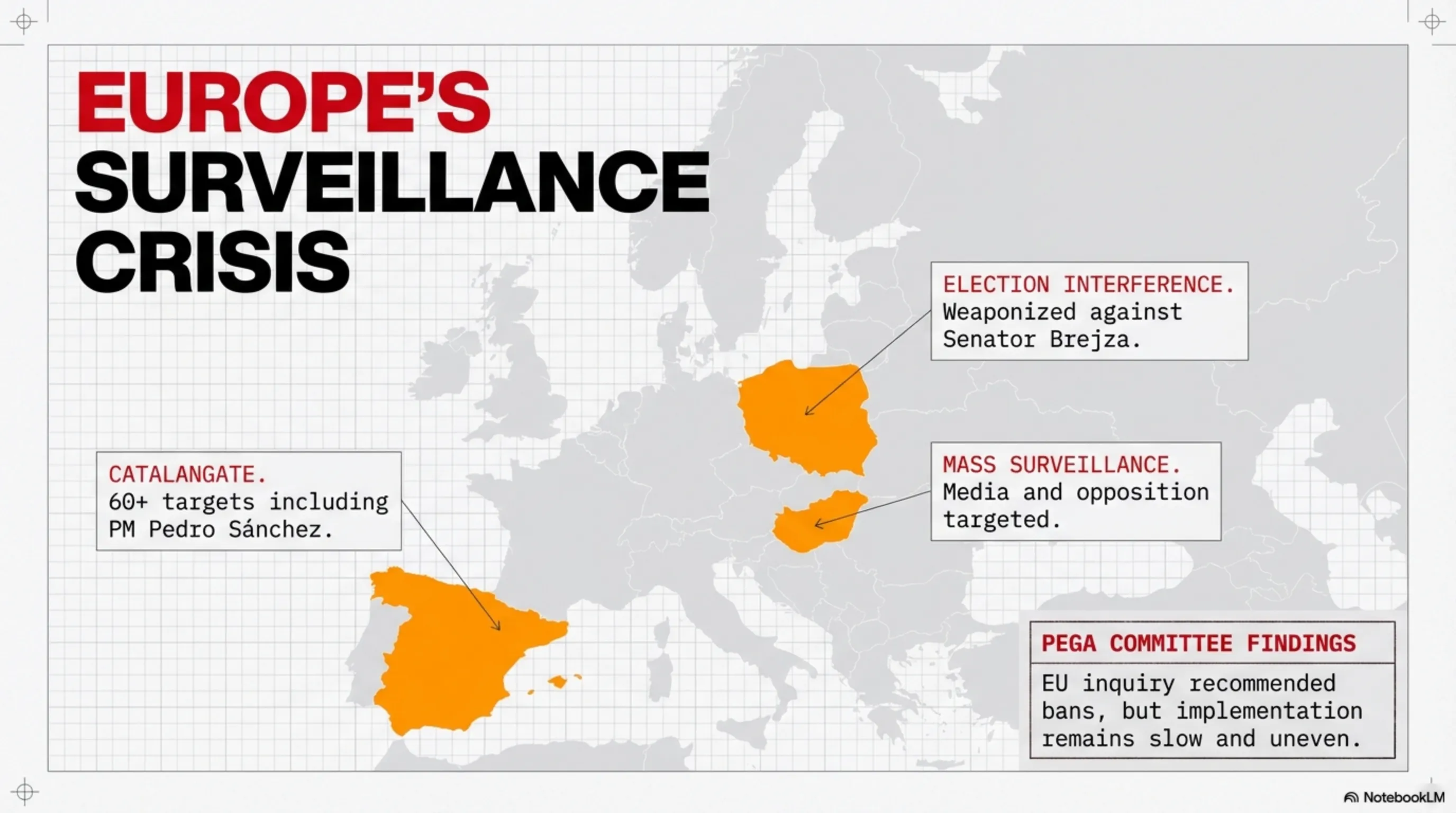
In 2022, the European Parliament launched an official inquiry committee called PEGA to examine the use of commercial spyware in member states. The results were shocking:
- Spain: Pegasus was used against Catalan independence leaders and even Prime Minister Pedro Sánchez
- Hungary: Pegasus was used against journalists, lawyers, and opposition politicians
- Poland: The government used commercial spyware against critics
The PEGA Committee recommended that spyware use against EU citizens should be prohibited except in specific cases with stringent judicial oversight. But implementation of these recommendations has been slow and uneven.
America: Sanctions and Confusion
American policy towards the spyware industry has been confused. The Biden administration imposed strict sanctions on Intellexa and NSO Group in 2024. But the Trump administration lifted some of these sanctions in December 2024.
Why this policy shift? Some analysts say the Trump administration wants better relations with Israel - where many of these companies are based. Others suggest the US government itself may want to use these tools.
Future Vision: The World of 2030 - Ubiquitous Surveillance?
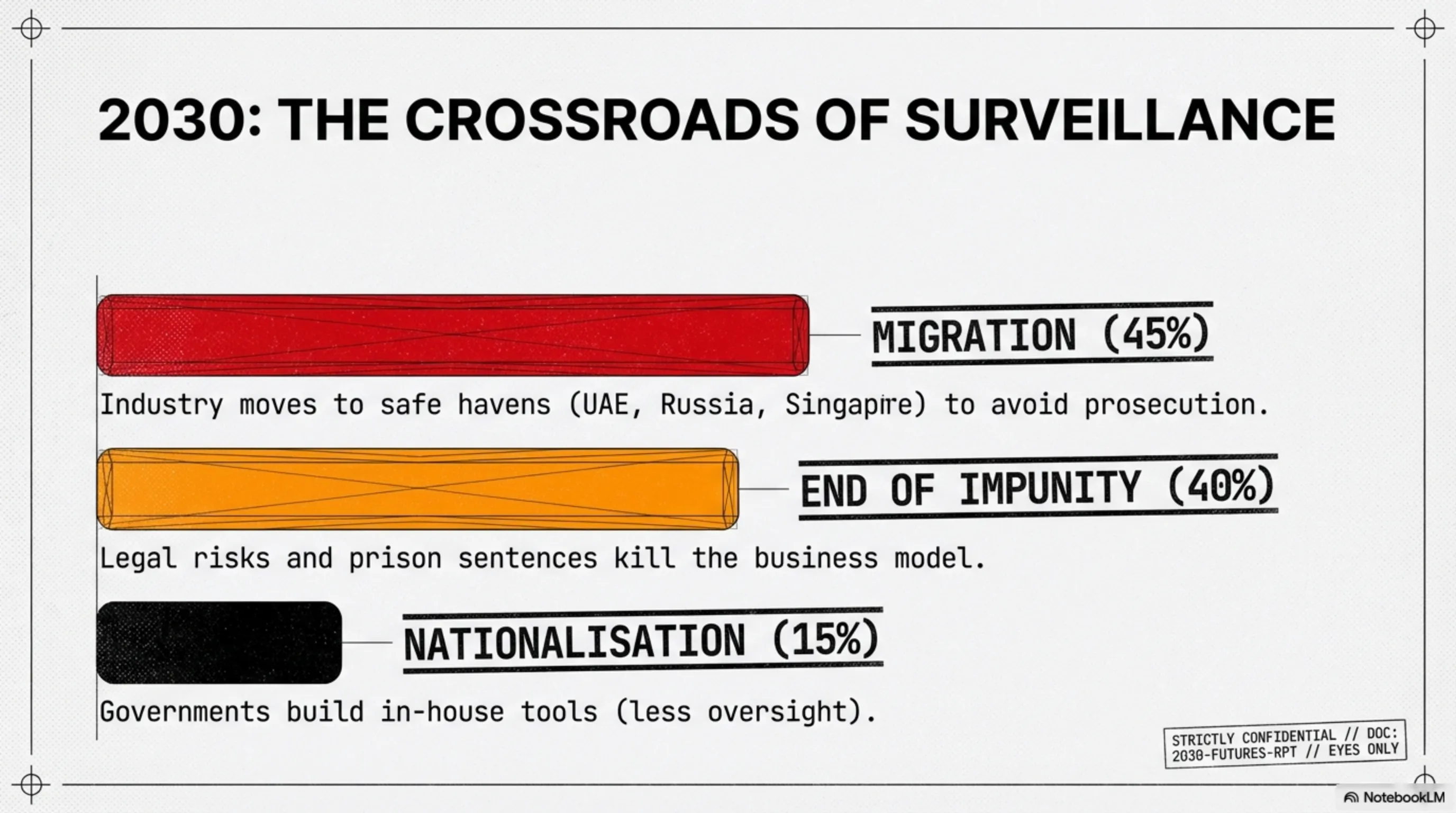
Scenario 1: End of the Impunity Era (Probability: 40%)
This verdict could initiate a new trend. If other courts also begin convicting spyware manufacturers, this industry may come under pressure. Companies may decide that legal risk does not justify the profit.
Scenario 2: Migration to Safe Jurisdictions (Probability: 45%)
The more probable scenario is that spyware companies migrate to countries with more lenient laws. For instance, some companies may relocate to UAE, Singapore, or even Russia.
Scenario 3: Nationalisation of the Industry (Probability: 15%)
The third scenario is that governments decide to build this technology themselves, rather than purchasing from private companies. This could be more dangerous, as there would be less oversight.
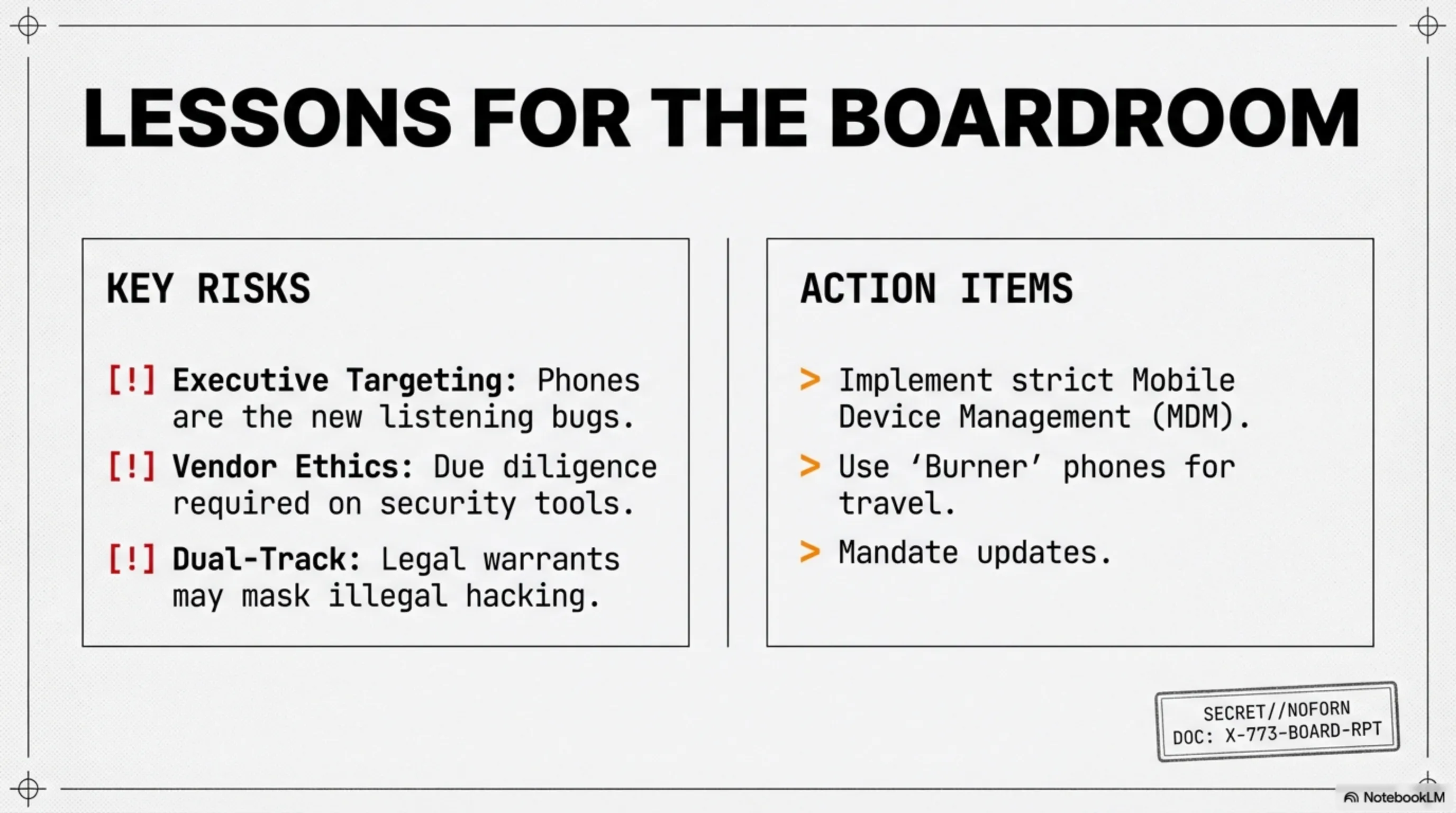
Security Lessons for Organisations
1. Mobile Devices Are High-Value Targets
Senior executives, board members, and key employees must assume their mobile devices may be targeted. Organisations should:
- Implement Mobile Device Management (MDM) systems
- Mandate regular operating system updates
- Use tools like Lockdown Mode
- Conduct regular security training for high-risk employees
2. Dual-Track Surveillance Is a Real Threat Model
The revelation that Predator victims were simultaneously under legal EYP surveillance shows that attackers may use legal and illegal methods in parallel. Organisations must assume that a legal wiretap warrant may coexist with an illegal hack.
3. Third-Party Risk Extends to Surveillance Vendors
Organisations procuring security tools - including network monitoring, intrusion detection, or intelligence services - must scrutinise vendor ethics, export control compliance, and sanction status.
Conclusion: Is This the End of the Impunity Era?
⚖️ Architect's Summary
Historic Verdict: For the first time in history, executives of a commercial spyware company were convicted for how their clients used the product. 126 years in prison for 4 individuals - this is a legal precedent.
Victims: 90+ politicians, journalists, and military officials in Greece. But Intellexa also sold to Sudan, Egypt, Vietnam, Angola, and Pakistan. This is a global industry.
Technology: Predator is Zero-Click spyware that can infect phones without any victim interaction. Camera, microphone, messages, calls - everything is accessible to the attacker.
The Final Question: Is this verdict the end of the impunity era, or merely an exception?
Predatorgate demonstrates that even the most powerful spyware companies can be prosecuted. But this is only a small victory. The commercial spyware industry continues to grow, and governments remain eager to purchase these tools.
As we saw in the Hardware Rebellion article, technology does not always benefit users. Sometimes, technology is used against us. The question is: can we reclaim control?
Tekin Army, in a world where privacy is becoming a luxury commodity, we must fight for our rights. This verdict is a beginning, but the road remains long.
The Broader Context: Europe's Spyware Crisis
Spain's Catalangate: A Warning Ignored
The Predatorgate scandal is not an isolated incident. In 2022, Spain faced its own spyware crisis when it was revealed that Pegasus had been used to target Catalan independence leaders. More than 60 individuals, including members of the European Parliament, had their phones infected.
But the scandal took an unexpected turn when it was discovered that even Prime Minister Pedro Sánchez and Defence Minister Margarita Robles had been targeted. This raised a disturbing question: if even the Prime Minister can be hacked, who is safe?
The Spanish government initially denied any involvement, but evidence suggested that the intelligence service CNI had purchased Pegasus. The scandal led to the resignation of the CNI director, but no criminal charges were filed. This is precisely what makes the Greek verdict so significant - it establishes criminal accountability where Spain failed.
Hungary's Surveillance State
Hungary under Viktor Orbán has become one of Europe's most prolific users of commercial spyware. Investigations by Citizen Lab and Amnesty International revealed that Pegasus was used against journalists, lawyers, opposition politicians, and even a Hungarian MEP.
The targets included investigative journalists from Direkt36 and Átlátszó, who were reporting on government corruption. One journalist, Szabolcs Panyi, discovered his phone had been infected multiple times over several years. The Hungarian government has never officially acknowledged using Pegasus, but the evidence is overwhelming.
What makes Hungary's case particularly concerning is the systematic nature of the surveillance. This was not targeting a few high-profile individuals; this was mass surveillance of anyone who challenged the government. It represents a fundamental threat to democracy.
Poland's Political Surveillance
In Poland, the previous government under the Law and Justice party (PiS) used commercial spyware against political opponents. The targets included Senator Krzysztof Brejza, who was running against the government in elections, and prosecutor Ewa Wrzosek, who was investigating government corruption.
The timing of the surveillance was particularly suspicious: Brejza's phone was infected during the election campaign, and hacked messages were selectively leaked to pro-government media to damage his reputation. This is not just surveillance; this is election interference using spyware as a weapon.
The new Polish government, elected in 2023, has launched investigations into the previous government's use of spyware. But as with Greece, the question remains: will anyone face criminal charges?
The Technology Arms Race: What Comes After Predator?
Next-Generation Spyware: AI-Powered Surveillance
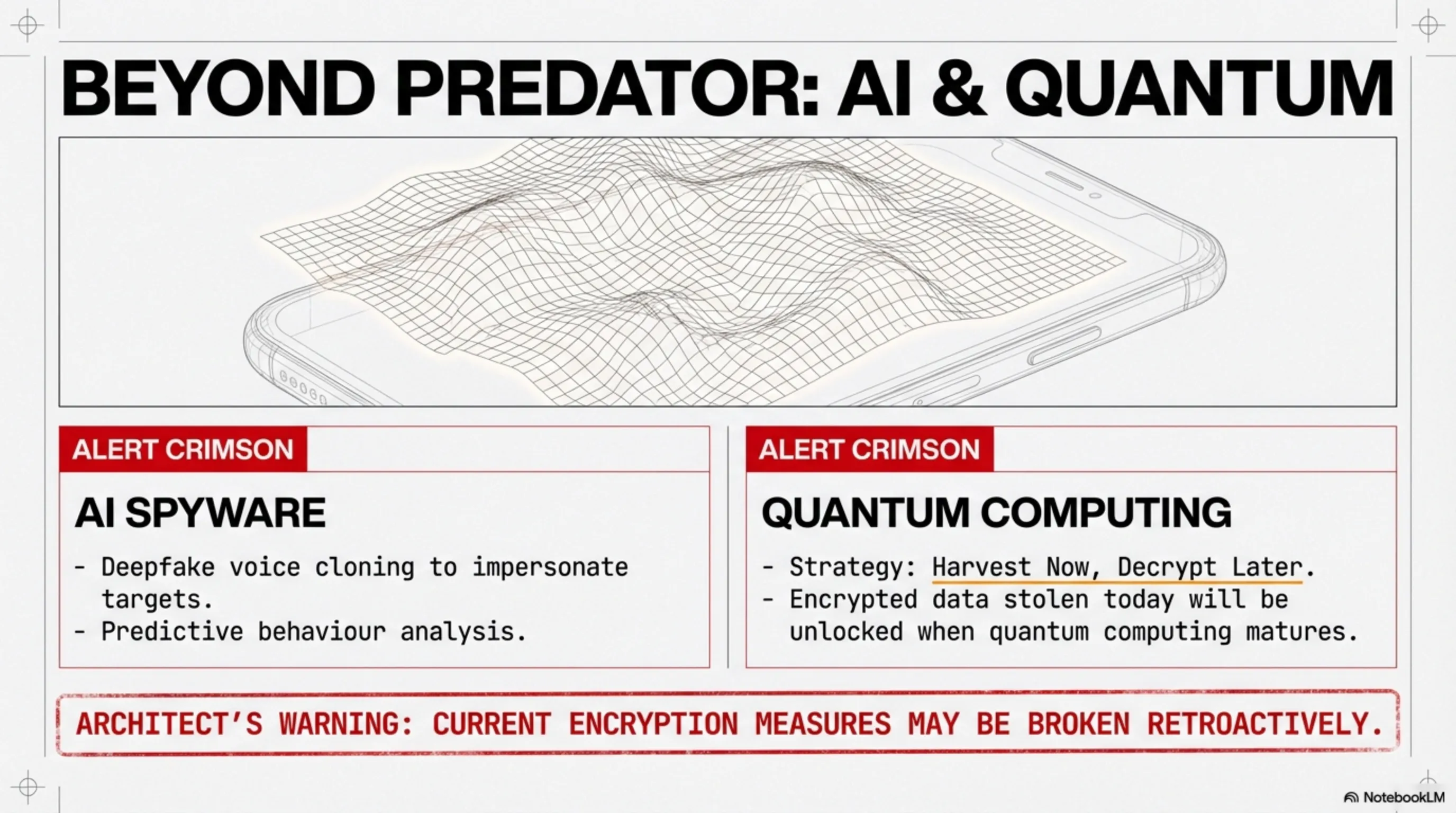
As we discussed in our article on Gemini 3.1 Pro and Agentic AI, artificial intelligence is transforming every industry - including surveillance. The next generation of spyware will likely incorporate AI capabilities that make current tools look primitive.
Imagine spyware that can:
- Automatically identify and extract sensitive information from your messages
- Predict your future actions based on your behaviour patterns
- Generate fake messages in your writing style to frame you
- Use voice cloning to impersonate you in phone calls
- Analyse your social network to identify other targets
This is not science fiction; these capabilities already exist in research laboratories. The question is not if they will be weaponised, but when.
Quantum Computing: The End of Encryption?
Another looming threat is quantum computing. Current encryption relies on mathematical problems that are extremely difficult for classical computers to solve. But quantum computers could potentially break these encryption schemes in minutes.
This means that even if your messages are encrypted today, an adversary could store them and decrypt them in the future when quantum computers become available. This is called "harvest now, decrypt later" - and intelligence agencies are already doing it.
The spyware industry is closely watching quantum computing developments. When quantum-resistant encryption becomes standard, spyware companies will need to adapt. But until then, they have a window of opportunity to harvest as much encrypted data as possible.
The Economic Model: Why Spyware Is So Profitable
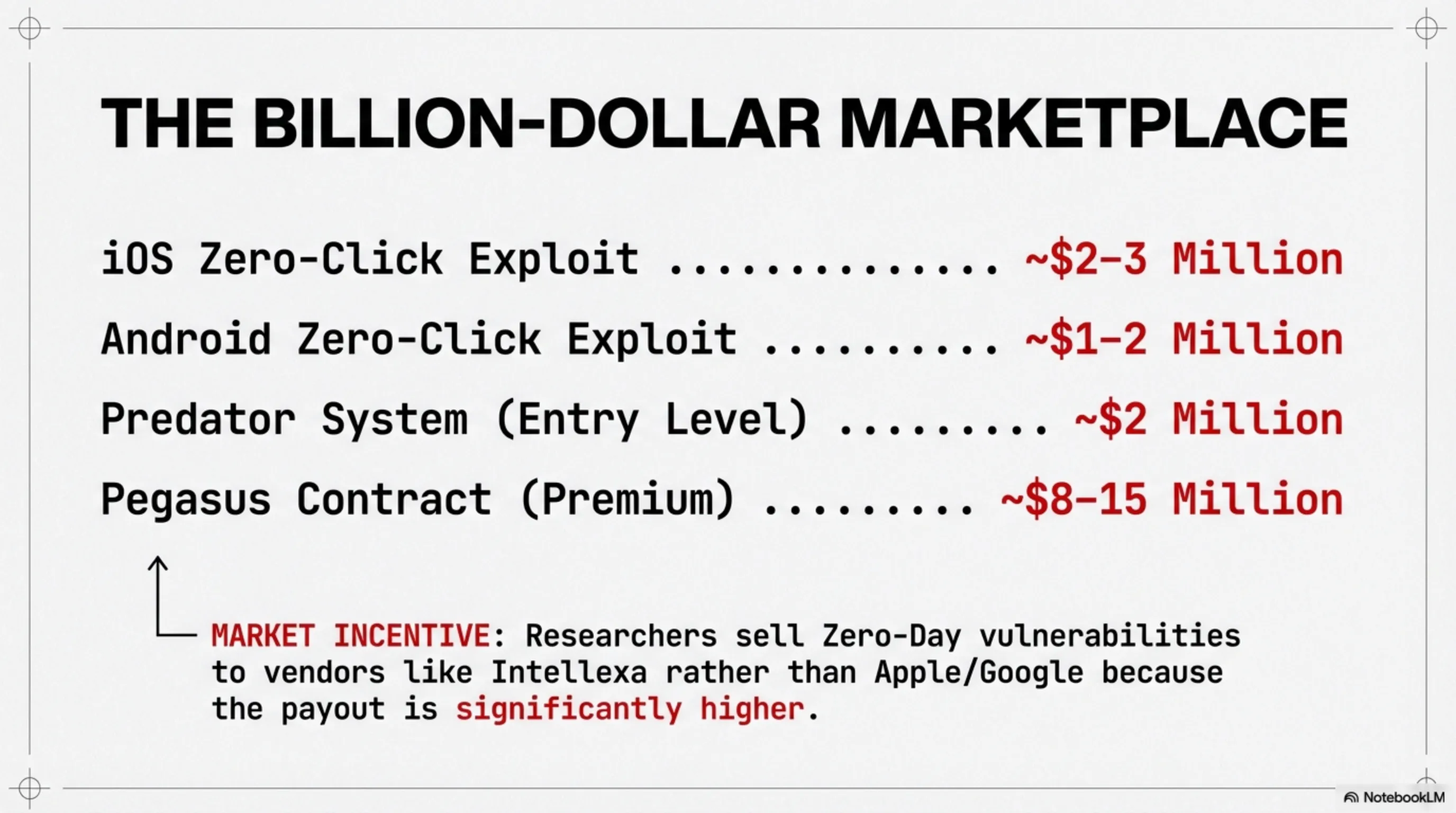
The Price List: What Does Surveillance Cost?
Leaked documents from NSO Group and other spyware vendors reveal the economics of this industry. A typical Pegasus contract costs between $8 million and $15 million for a government client. This includes:
- Licences to infect up to 50 devices simultaneously
- Technical support and training
- Regular updates with new exploits
- Forensic analysis tools to examine harvested data
For smaller budgets, companies like Intellexa offer more affordable options. Predator contracts reportedly start at around $2 million for basic capabilities. This makes surveillance accessible to countries that cannot afford Pegasus.
The profit margins are extraordinary. The actual cost of developing and maintaining spyware is relatively low compared to the prices charged. This is why the industry continues to grow despite legal and reputational risks.
The Exploit Market: Zero-Days for Sale
A crucial component of the spyware industry is the market for zero-day vulnerabilities. These are bugs in software that are unknown to the vendor and therefore have no patch available. They are extremely valuable because they allow guaranteed infection.
The prices for zero-days vary depending on the target platform:
- iOS zero-click exploit: $2-3 million
- Android zero-click exploit: $1-2 million
- WhatsApp zero-click exploit: $1.5-2.5 million
- Windows zero-day: $100,000-500,000
Spyware companies either develop these exploits in-house or purchase them from independent researchers. This creates a perverse incentive: instead of reporting vulnerabilities to vendors so they can be fixed, researchers sell them to the highest bidder.