In 2026, personal cybersecurity has entered an era of absolute paranoia. This deep analytic teardown (exceeding 2,500 words) dissects the anatomy of Zero-Click Exploits, the insidious nature of Pegasus 4.0 surveillance malware, and the terrifying intelligence agency tactic known as "Harvest Now, Decrypt Later" (HNDL). We will examine exactly how Apple and Signal are combating next-generation quantum computers by deploying Post-Quantum Cryptography (PQC) protocols like PQ3. This document serves as a severe structural warning for journalists, go
Zero-Click Exploits and Quantum Encryption: The New Arms Race in Mobile Security
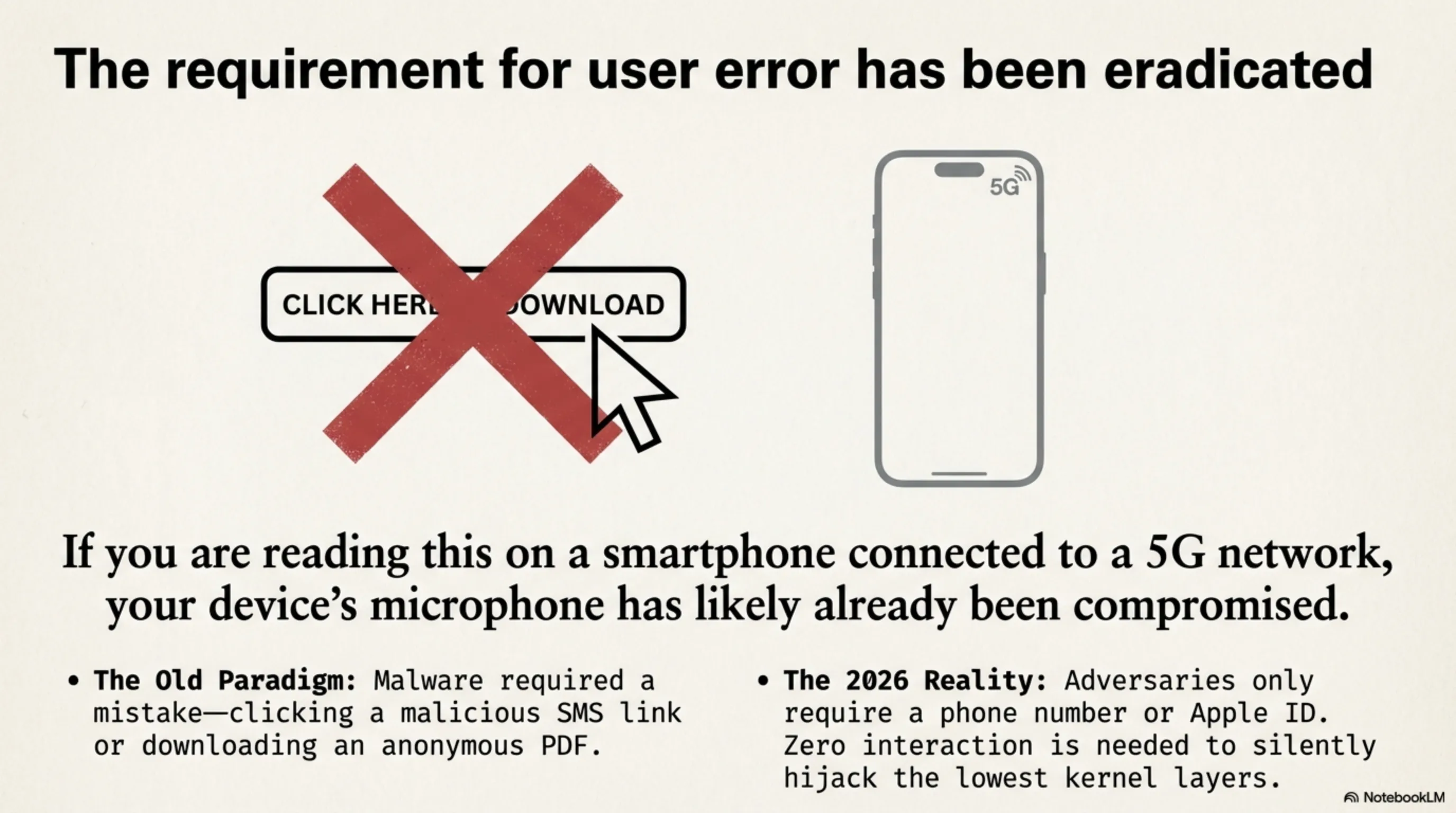
Welcome to the Tekin Security Briefing. Today is March 5, 2026. If you are currently reading this text on a smartphone connected to a 5G network, your device’s microphone has likely already been compromised. In the not-so-distant past, for a device to be infected by malware, the victim had to make a "mistake"—like clicking a malicious phishing link in an SMS or downloading an anonymous PDF. In 2026, that requirement has been entirely eradicated. With the rise of "Zero-Click" attacks, the adversary doesn't need you to interact at all. They merely require your phone number or Apple ID to silently hijack the lowest kernel layers of your device. In this highly technical teardown, we analyze the modern anatomy of cyber defense and attack mechanisms.
Strategic Layer 1: The Invisible Monster — Zero-Click Architecture
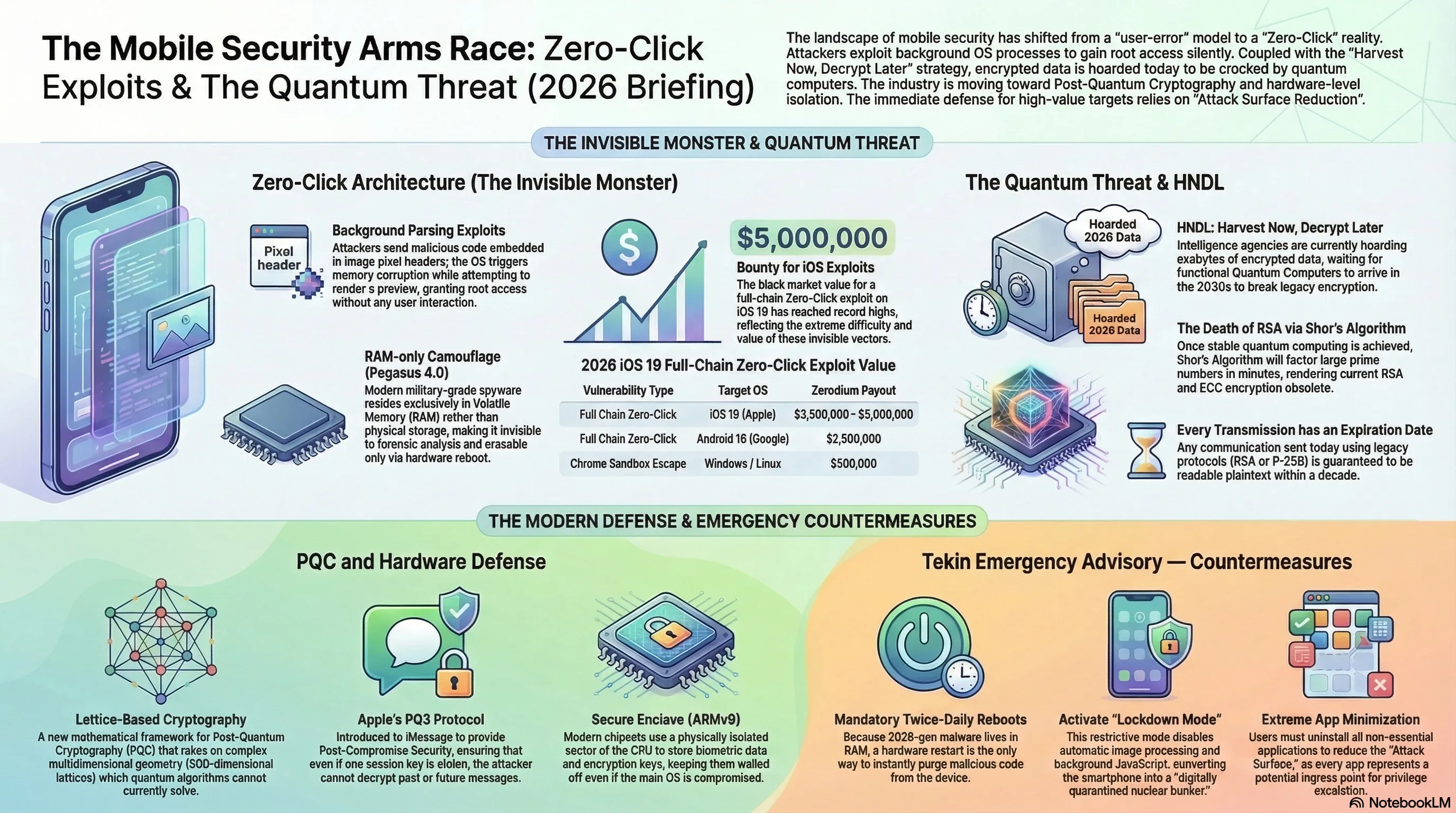
The concept behind a Zero-Click attack relies on exploiting background OS processes that run autonomously without waiting for user interaction. Your phone is constantly pre-processing inbound data so that it’s immediately available the moment you illuminate the screen. This exact utility is the Achilles heel of modern security.
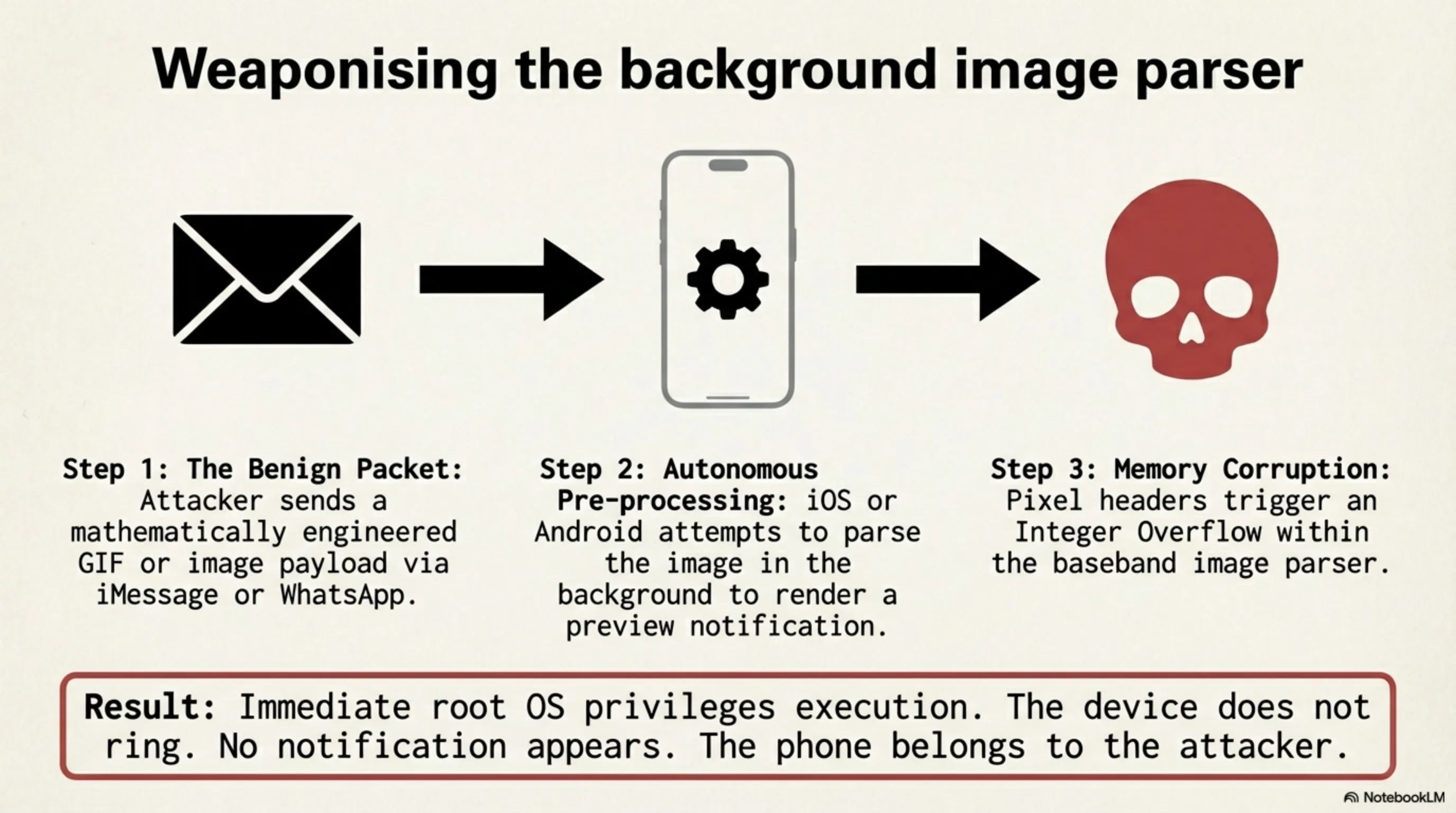
1.1 Penetrating the Image Processing Baseband
The most notorious Zero-Click vectors (such as Apple’s infamous FORCEDENTRY exploit) are deployed via messaging protocols like iMessage or WhatsApp. An attacker sends a seemingly benign GIF or image packet. The operating system (iOS or Android) automatically attempts to parse this image in the background to render a tiny preview notification. If that image file has malicious code mathematically engineered into its pixel headers, it triggers an Integer Overflow or Memory Corruption within the image parser. The attacker's payload executes with root OS privileges immediately. The phone in your pocket doesn't ring or notify you; the device simply belongs to the attacker.
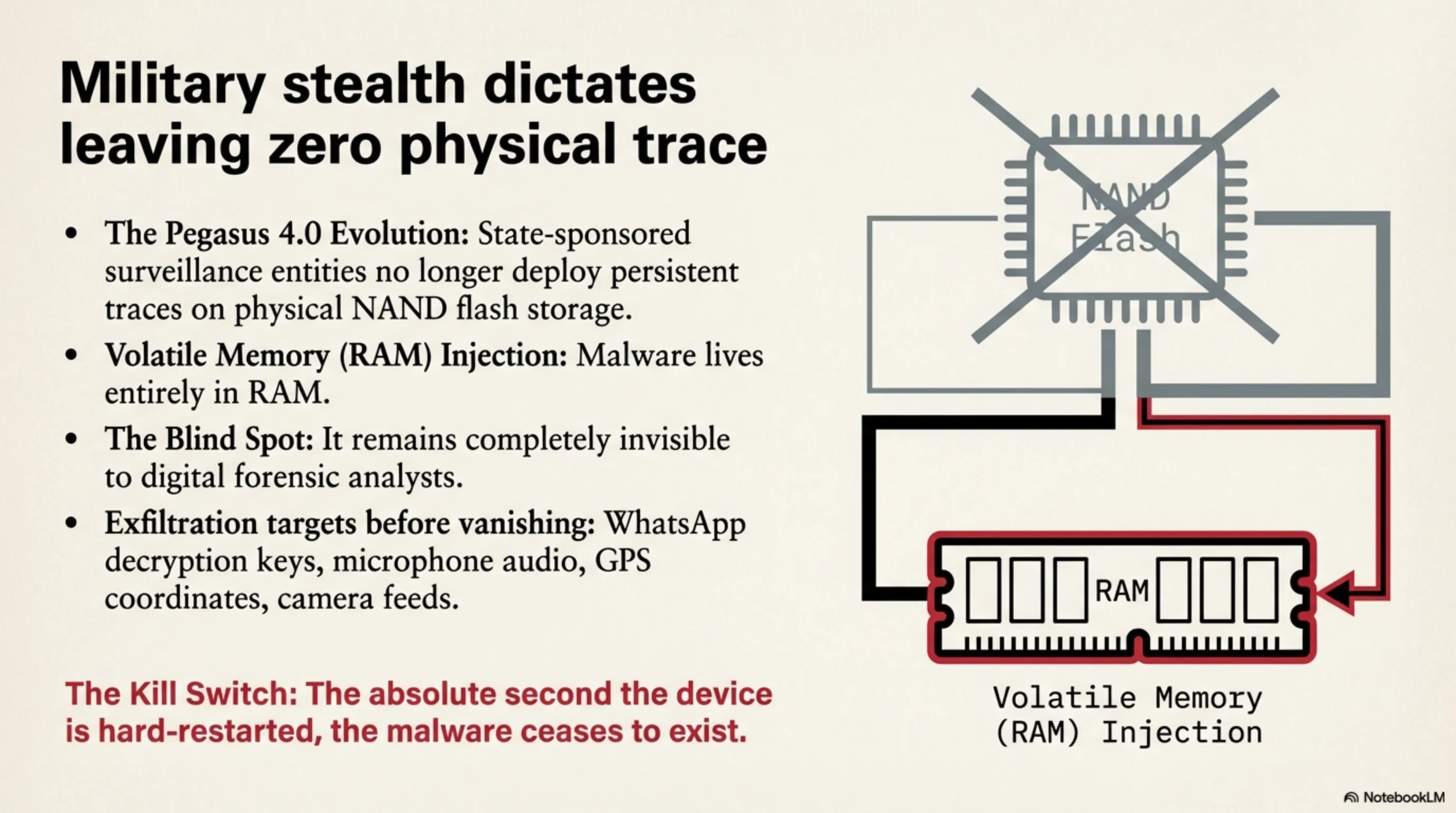
1.2 Pegasus 4.0 Evolution: RAM-only Camouflage
State-sponsored surveillance entities, such as the NSO Group (creators of Pegasus), have elevated this malware to an unprecedented level of military stealth. The 2026 iterations of these spyware suites no longer leave persistent traces on the device's physical NAND flash storage. Instead, they deploy entirely into Volatile Memory (RAM). This means the absolute second you hard-restart your phone, the malware ceases to exist, making it entirely invisible to digital forensic analysts. However, during its brief lifecycle, it has already exfiltrated your microphone audio, GPS coordinates, camera feeds, and WhatsApp decryption keys.
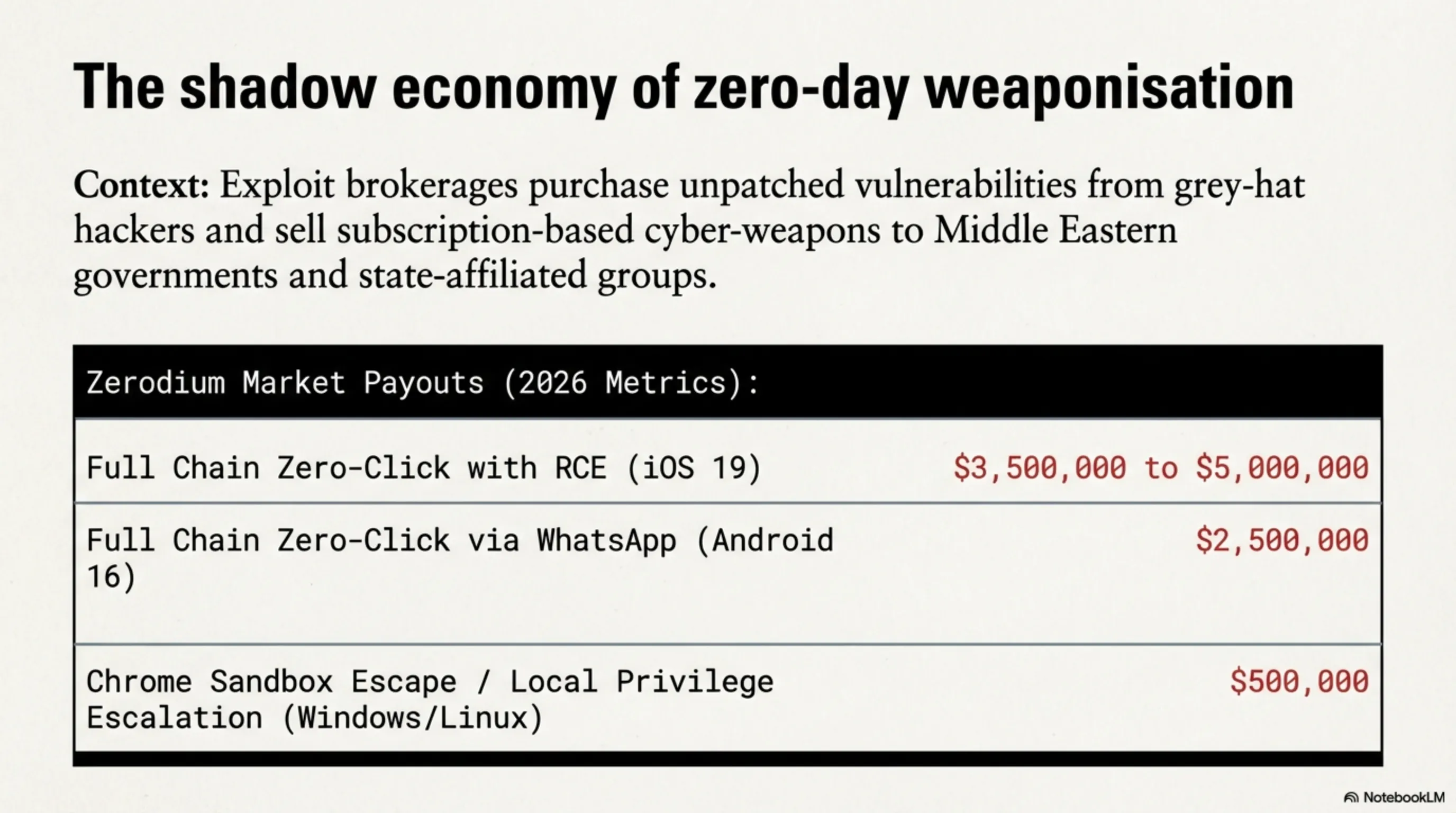
📊 Strategic Graphic: Black Market Value of Exploits (2026 Metrics)
| Vulnerability Type | Target OS | Zerodium Payout (Est. USD) |
|---|---|---|
| Full Chain Zero-Click with Remote Code Exec (RCE) | iOS 19 (Apple) | $3,500,000 - $5,000,000 |
| Full Chain Zero-Click via WhatsApp Payload | Android 16 (Google) | $2,500,000 |
| Chrome Sandbox Escape / Local Privilege Escalation | Windows / Linux | $500,000 |
Strategic Layer 2: The HNDL Protocol (Harvest Now, Decrypt Later)
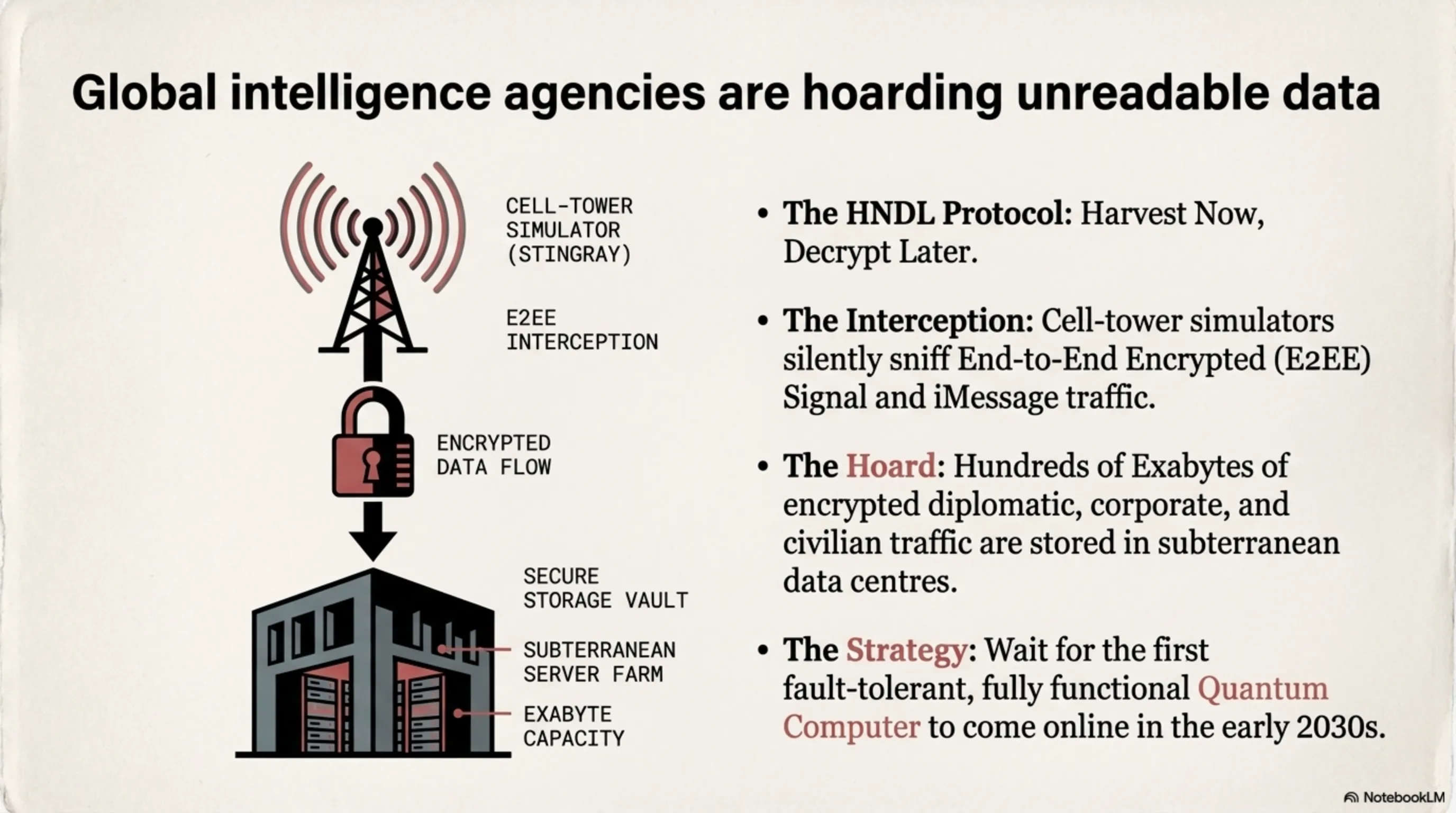
You may incorrectly assume that because your iMessage or Signal chats feature End-to-End Encryption, even if they are sniffed by cell-tower simulators (Stingrays) handled by intelligence agencies, they remain unreadable gibberish. Indeed, mathematically, classical RSA and Elliptic Curve (ECC) algorithms cannot be broken by current supercomputers before the heat death of the universe.
2.1 Why Intelligence Agencies Archive Encrypted Traffic
However, global intelligence agencies are executing a terrifying geopolitical strategy known as **HNDL (Harvest Now, Decrypt Later)**. They do not need to read your encrypted data today. Instead, they intercept and hoard hundreds of Exabytes of encrypted diplomatic, corporate, and private civilian traffic within subterranean data centers. Their entire strategy is predicated on waiting for the first fault-tolerant, fully functional Quantum Computer to come online in the early 2030s.
2.2 The Mathematical Death of RSA (Shor's Algorithm)
The very minute a stable Quantum Computer is powered on, Shor’s Algorithm will be utilized to factor exponentially large prime numbers (the bedrock of current internet encryption) in a matter of minutes. On that day, every single archived piece of data from the past decade—bank routing passwords, private WhatsApp extramarital affairs, classified defense emails—will suddenly become readable plaintext. This is not a theoretical threat; it is a mathematical guarantee.
Cryptographic Warning: Every communication transmission you initiate today utilizing legacy RSA or P-256 protocols carries a functional expiration date. Within a decade, those who harvested it will unconditionally read it.
Strategic Layer 3: The Quantum Shield (Post-Quantum Cryptography)
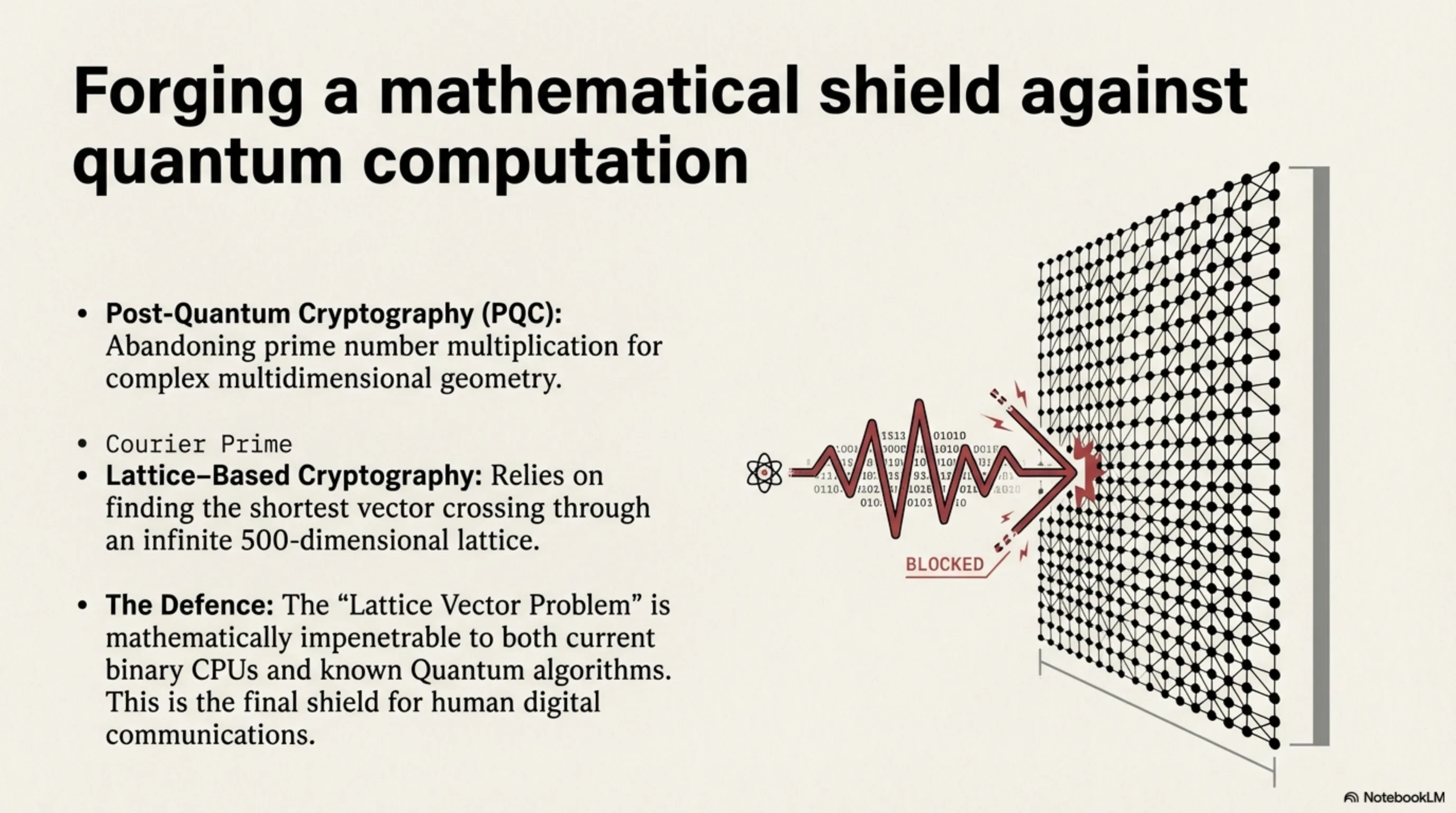
The global software engineering community has not been passive. A massive race has precipitated to design completely novel mathematical frameworks that even Quantum Computers cannot untangle.
3.1 Lattice-Based Cryptography
Instead of relying on multiplying massive prime numbers, Post-Quantum Cryptography (PQC) relies on incredibly complex multidimensional geometry. Finding the shortest vector crossing through an infinite 500-dimensional lattice (the Lattice Vector Problem) is a mathematically hard problem that neither binary CPUs nor known Quantum algorithms can currently solve. This intense computational mathematics will serve as the final shield for human digital communications.
3.2 Analyzing Apple's iMessage PQ3 Standard
Apple recently activated the PQ3 protocol globally across iMessage, introducing the most substantial cryptographic security upgrade in the company's messaging history. Signal protocol developers enacted similar standards. Within the PQ3 framework, even if a highly sophisticated attacker compromises an active session key, the protocol constantly rotates keys using quantum-resistant formulas (a property known as Post-Compromise Security), ensuring the attacker cannot decrypt past or future messages within the same chat tunnel.
Strategic Layer 4: Hardware vs. Software Defense
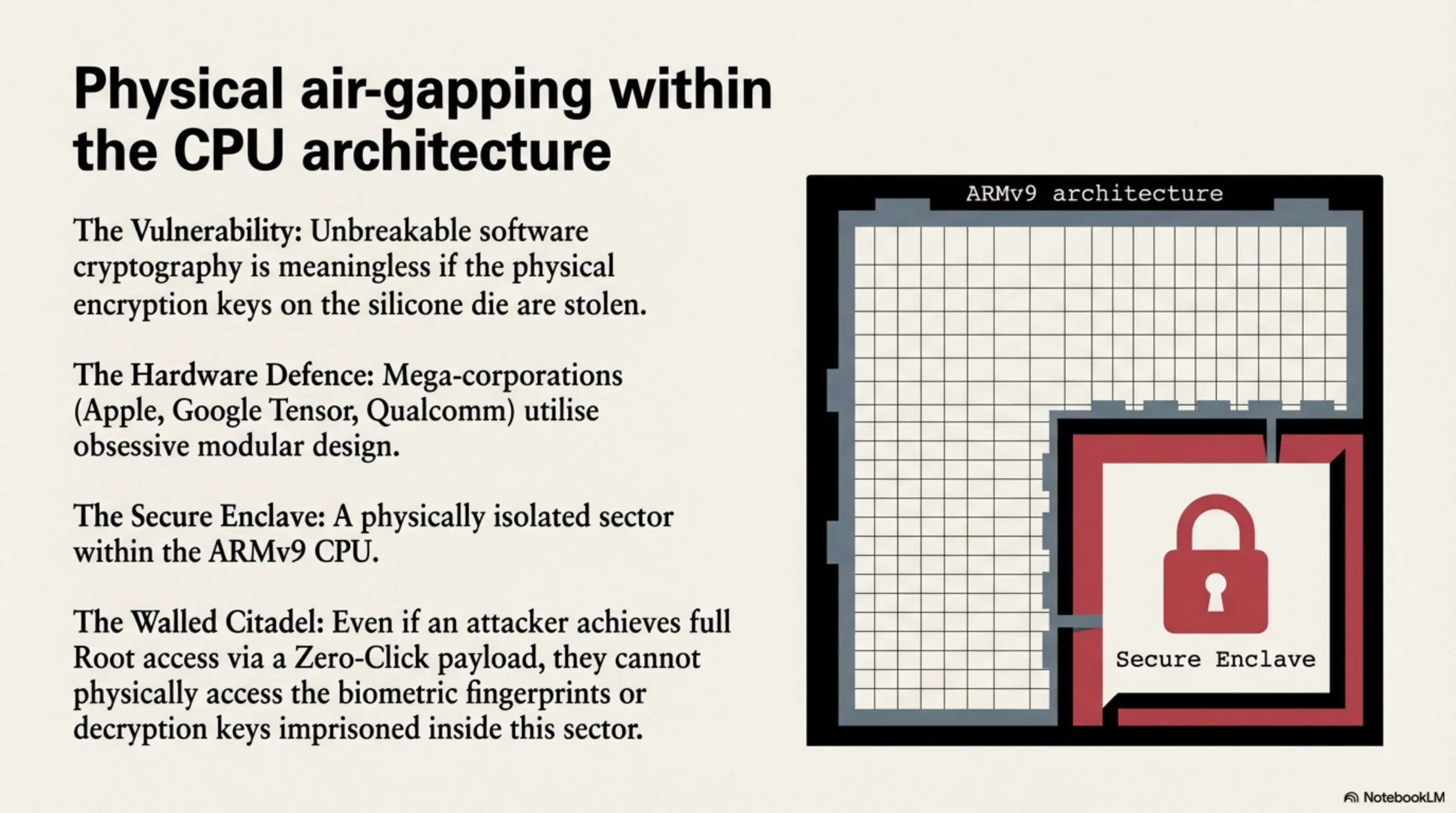
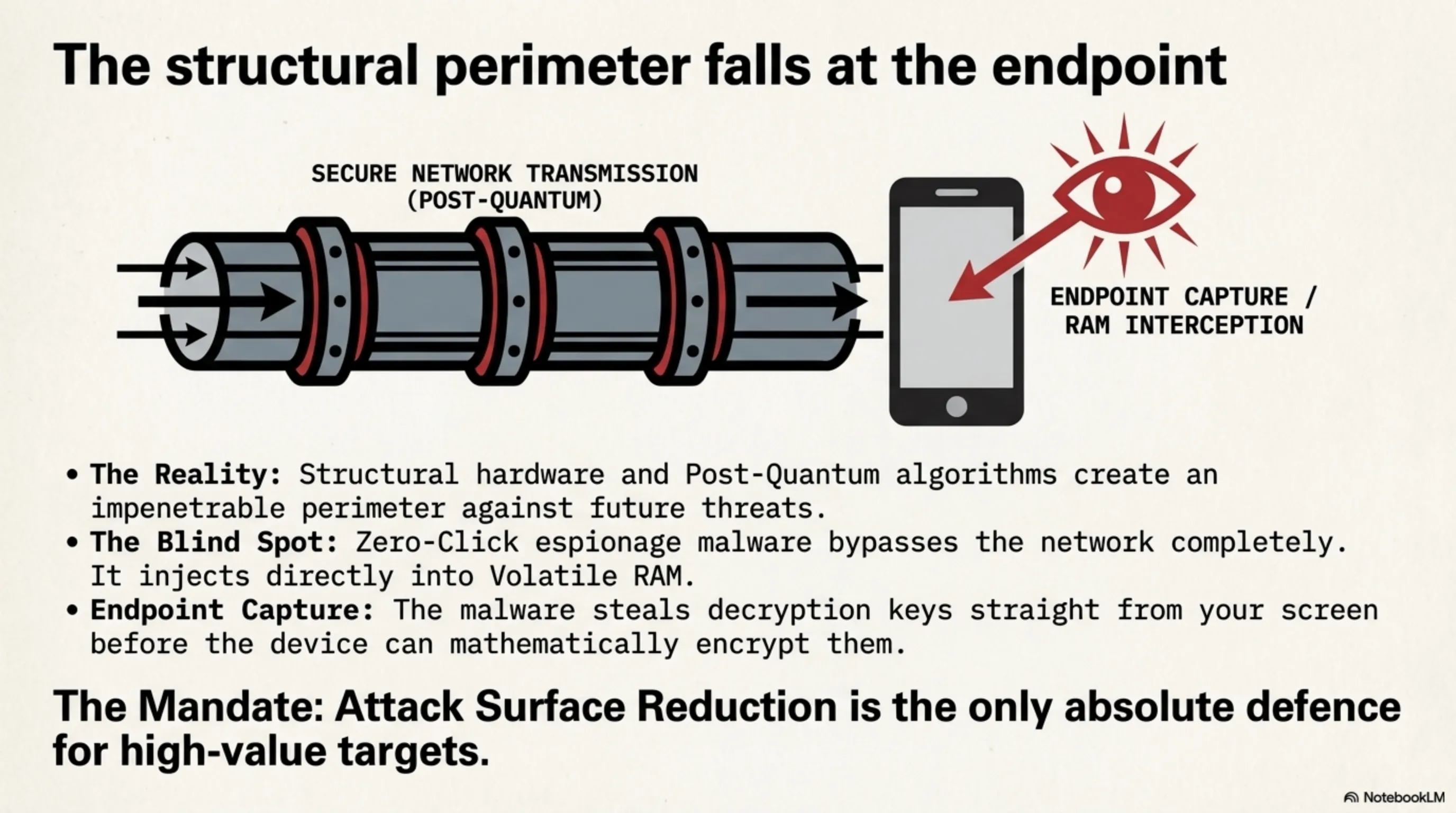
Unbreakable software cryptography is completely meaningless if the physical encryption keys stored inside the silicone die are compromised.
4.1 Physical Air-gapping in ARMv9 Architecture
Mega-corporations like Apple, Google (Tensor), and Qualcomm design their chipsets to be obsessively modular. A dedicated, physically isolated sector known as the Secure Enclave exists internally within the CPU, which the primary iOS or Android operating system cannot access directly. Even if an attacker achieves full Root access via a Zero-Click payload, they remain physically walled off from extracting the biometric fingerprints or decryption keys imprisoned inside this fortified citadel.
Strategic Layer 5: Geopolitics of the Cyber Black Market
In volatile geopolitical zones like the Middle East, where political and security tensions are at a perpetual boiling point, the smartphones of senior oil executives, investigative journalists, and civil rights activists are the primary targets of military-grade espionage malware.
5.1 The Multimillion-Dollar Zero-Day Brokers
A shadowy industry of exploit brokerages exists that purchases unknown, unpatched Apple and Android vulnerabilities from grey-hat hackers at prices ranging from $500,000 to $5,000,000 per exploit chain. These entities then package these cyber-weapons into subscription-based software suites and sell them to Middle Eastern governments, security apparatus organizations, and state-affiliated client groups. This underground economy is extraordinarily profitable and operates in a legal grey zone completely devoid of international oversight.
5.2 Strategic Defensive Measures for High-Risk Targets
For individuals at elevated risk (journalists, diplomats, corporate executives in the energy sector), the ultimate recommendation is the activation of Apple's restrictive **Lockdown Mode**. This mode physically disables automatic image processing in iMessage, blocks background JavaScript JIT compilation in Safari, prevents USB connections to unknown devices, and converts the device into a digitally quarantined nuclear bunker. Attack Surface Reduction is the only absolute defense against Zero-Click vectors.
Strategic Layer 6: Engineering Countermeasures — Attack Surface Reduction Protocol
Understanding the depth of structural mobile vulnerabilities in 2026, security engineers have distilled their defensive posture into a multi-layered defensive checklist designed to minimize the exploitable attack surface to an absolute minimum.
6.1 Mandatory Daily Hardware Reboots
Since 2026-generation malware resides exclusively in volatile RAM, a simple hardware restart purges all malicious code instantly. The engineering recommendation from Tekin is unambiguous: high-value targets must hard-reboot their primary device at minimum twice daily. For ultra-sensitive communications, a dedicated secondary air-gapped device that has never connected to any network remains the only 100% guaranteed solution.
6.2 Application Surface Minimization
Every installed application is a potential ingress point for sophisticated attackers. The smallest vulnerability in a game or social media app can initiate a chain of Privilege Escalation leading to full Kernel compromise. Aggressive removal of non-essential applications, combined with immediate installation of security patches the moment they are released, constitutes the cheapest and most effective defensive shield available to any digital citizen.
Tekin Emergency Advisory: If you are a journalist, civil rights activist, or government official, activate Lockdown Mode today, uninstall all non-essential applications, and reboot your device twice daily. This is the simplest layer of defense and neutralizes 90% of known attack vectors.
⚖️ Tekin Official Defensive Verdict
In the cyber-geopolitical atmosphere of 2026, the illusion of absolute privacy has evaporated. A flagship smartphone is inherently a highly advanced military tracking node that you willingly carry. While the transition by tech behemoths toward Post-Quantum algorithms (like Apple's PQ3) creates an impenetrable mathematical perimeter against future Quantum computation, the immediate threat vector lies in Zero-Click spyware. Because espionage malware bypasses the network completely and injects directly into Volatile RAM, it steals decryption keys straight from the End-Point (your screen) before mathematically encrypting them. The absolute only defense for high-value targets (C-Suite executives and diplomats) is to enforce extreme 'Attack Surface Reduction' via restrictive OS Lockdown Modes, utilize secondary air-gapped devices, execute daily hardware reboots, and accept the grim reality that an invisible process is perpetually monitoring their existence.