Executive Briefing: Strategic Analysis of the January 2026 Cyber Crisis January 2026 began with a storm of cyber attacks that signify a fundamental paradigm shift in hacker strategies. The major transformation we witnessed this month was the transition from purely financial attacks to paralyzing critical infrastructure and service chains—including hospitals, energy distribution networks, and food supply lines. In this section, we have provided a concise summary of what you will read in this comprehensive 2000-word article, so that even if you don't have time for a full read, you won't fall behind the pulse of global security. Our goal here is to introduce you to the real dimensions of the lurking crisis and provide the necessary technical context to navigate it. The first alarm sounded in mid-January with a massive hack of one of the world's largest retail chains. The leak of data for over 40 million customers worldwide was not just a privacy disaster, but an economic shock to the stock market. However, the most tragic incident involved the "BlackByte v3" ransomware, which targeted navigation systems and electronic health records of five major hospitals in Europe and Asia, disrupting medical treatments for hours. These attacks proved that in 2026, hackers are no longer just after your credit card; they are after the pulse of your daily life. In this environment, distinguishing between truth and forgery has become the toughest challenge for IT managers. Tekin Plus analysis shows that generative AI has now become the primary tool for criminal groups. Advanced phishing, which we examine in this report, is no longer limited to deceptive emails; it includes sophisticated audio and video deepfakes that fool even experienced executives. AI has enabled hackers to design attacks that are both scalable and highly personalized, making traditional security barriers look obsolete. We saw how Large Language Models were used this month to discover security vulnerabilities in legacy systems that had gone unnoticed for years. Ultimately, the purpose of this report is not just to inform, but to provide a lighthouse for small businesses and everyday users to find their safe harbor in this turbulent ocean. In the following article, we introduce three core survival strategies: implementing Zero Trust architecture, multi-layered security, and continuous organizational culture building. From offline backups to modern identity management, all the necessary tools are detailed in depth. Join us as we start 2026 with security and refuse to let your digital assets become prey for the new generation of hackers.
The digital world of 2026 bears little resemblance to previous years. The pace of technological progress has created as many deep vulnerabilities as it has opportunities. Our comprehensive January 2026 report reveals a new generation of hackers—"fast, smart, and ruthless"—who utilize tools like early quantum computing and autonomous AI to breach defenses. In this analytical report, we dissect recent attacks and explore the paths out of this global crisis. The depth of this content is designed to help you grasp every hidden dimension of these threats.
1. An Anatomy of the January 2026 Megabreaches

The month of January was hit by incidents that sent shivers down the spines of IT managers in global organizations. We witnessed how physical and digital security have become inextricably linked. In this section, we explore the three main categories of attacks that caused the most significant damage.
Advanced Phishing & The Rise of Deepfake Fraud 2.0
The days of "you've won a prize" emails are long gone. In January 2026, hackers utilized AI to perform sophisticated Voice Cloning of CFOs and executed fraudulent wire transfers via deepfaked video calls. This attack type, known as "CEO Fraud 2.0," has recorded a staggering 85% success rate in organizations lacking hardware-based multi-factor authentication. Imagine your CEO talking to you on a video call; their lip movements and eye contact are perfectly natural, and they request an urgent funds transfer for a deal. For an average employee, detecting the forgery is nearly impossible.
Tekin Plus research indicates that these attacks are proliferating due to the accessibility of cheap AI tools on the dark web. Hackers use just a few seconds of a manager's voice recorded from social media to build a full vocal model. This is where the importance of out-of-band verification protocols becomes paramount. Companies must learn that in the age of deepfakes, "seeing" is no longer "believing."
Ransomware: Targeting the Lifelines of Humanity
The attack on healthcare networks during the third week of January pushed the ethical boundaries of hacking. The ransomware group known as "MedLock" encrypted critical data, robbing doctors not just of money, but of time. In this attack, hackers demanded $50 million in Bitcoin. The sobering reality was that many of these hospitals were running legacy software that hadn't seen a security patch in years.
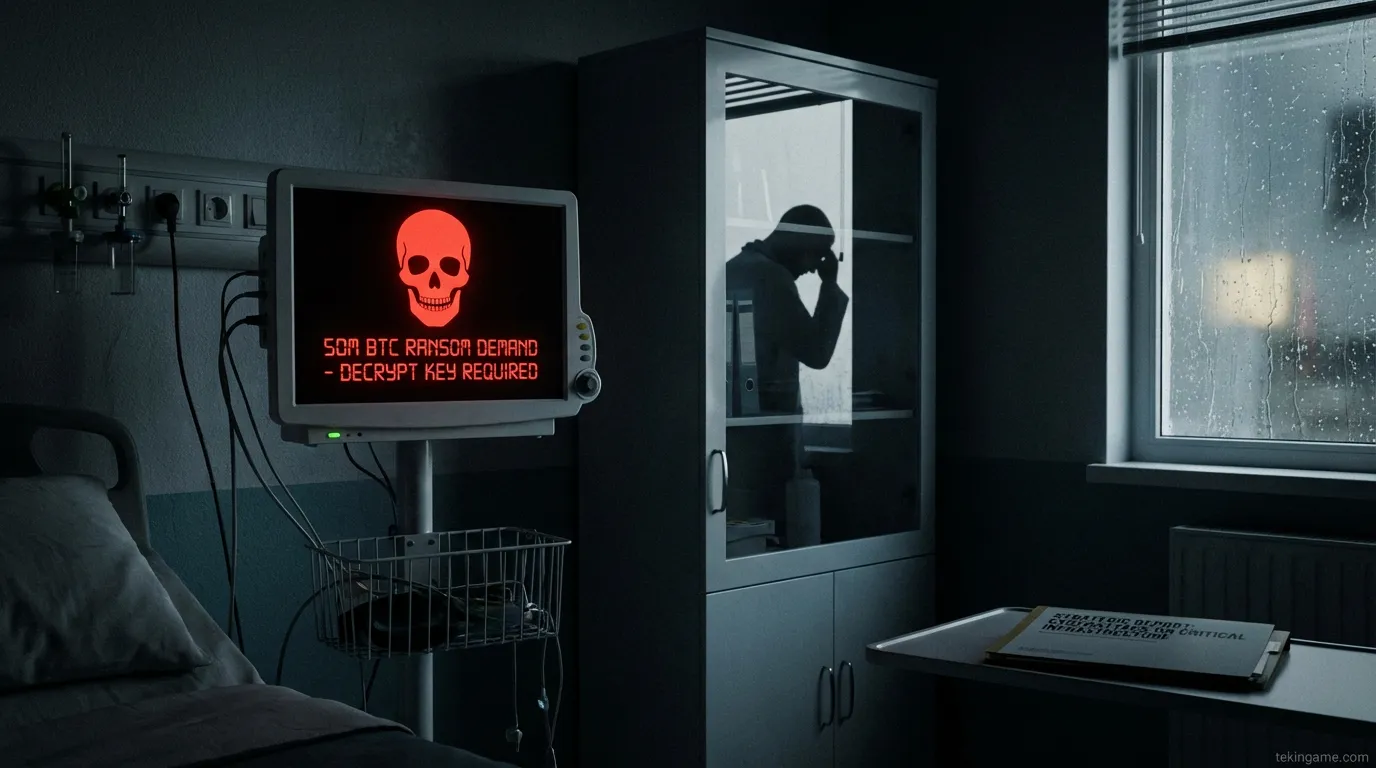
Beyond the financial impact, the freezing of smart surgical tools and the loss of Electronic Health Records directly endangered patient lives. This type of attack signifies the rise of "Digital Terrorism." In 2026, ransomware doesn't just lock your files; it cuts off your organization's oxygen. Combatting this phenomenon requires more than just software updates; it needs a comprehensive, multi-dimensional crisis management strategy involving global security agencies and ultra-fast recovery systems.
The Supply Chain Trap: Infiltrating Through Trusted Channels

Hackers are no longer just attacking the main fortress; they are attacking the Trojan horses that the fortress trusts. By injecting malicious code into open-source software libraries used by millions of developers, hackers were able to breach thousands of companies simultaneously without triggering alarms. The disaster that hit a major cloud platform in late January was a direct result of this type of infiltration.
We found that many companies incorporate ready-made code into their projects without comprehensive security vetting. This blind trust has created a golden opportunity for state-sponsored hackers and criminal syndicates. Supply Chain Security is now the top priority for those who want to prevent unwanted intruders in their systems. You must know the origin of every line of code and use verified digital signatures to confirm file integrity.

2. The Strategic Shift: Why 2026 is Different
You might ask: weren't there attacks in previous years? The fundamental difference lies in computing power and targeting precision. With the emergence of early quantum processors capable of breaking traditional encryption, hackers have become bolder. Moreover, automated exploitation allows a single hacker to scan and breach thousands of targets a day. At Tekin Plus, we see hackers using AI-driven botnets that, upon entry, immediately begin analyzing the network to find the most valuable data.

Critical Infrastructure Under Pressure
In January 2026, we saw power distribution grids in certain regions being targeted. These attacks were not for ransom but to paralyze a region's economy. By infiltrating Industrial Control Systems (ICS), hackers were able to manipulate voltage settings and cause physical damage to transformers. This proves that the boundary between cyberspace and physical reality has completely vanished.
The Global Impact and Economic Fallout
The economic ripple effects of these attacks have been felt globally. Market volatility increased as trust in digital transactions wavered. Large corporations are now forced to allocate up to 30% of their tech budget solely to defensive measures. The "cyber-insurance" market is also undergoing a radical transformation as insurers demand stricter adherence to modern security frameworks.

3. Deep Dive Case Study: The GlobalMart IoT Heist
One of the most intriguing and terrifying cases of January involved GlobalMart. Hackers entered the system through a "backdoor" in inventory management software developed by a third-party vendor. They remained undetected in the network for three weeks, extracting purchasing patterns and sensitive customer data. This incident taught us that even if your own security is excellent, the security of your business partners is equally critical.

4. The Tekin Plus Defensive Blueprint: 2026 Edition
In the face of these orchestral attacks, what must be done? The Tekin Plus security team, after analyzing dozens of cases in January, has three vital recommendations that must be prioritized today.

Pillar I: Air-Gapped and Immutable Data Repositories
Backing up to the cloud is good, but it's no longer enough. You need a "Cold Storage" or offline version that is never connected to any network. 2026 hackers first find and destroy your online backups to force a ransom payment. Having a separate set of drives that only connect once a week for replication is your ultimate savior. Furthermore, using immutable repository technology ensures that even if a hacker reaches the backup system, they cannot delete or encrypt existing data. This is your final stand against total digital destruction.

Pillar II: Hardware-Based 2FA and FIDO2 Standards
SMS-based security codes are obsolete due to SIM Swapping. We recommend using hardware security keys (like YubiKey) or authenticated apps. This creates a solid barrier against 99% of phishing attacks. In 2026, a password alone is like a plastic lock; you need a physical layer that a hacker cannot steal remotely. Biometric authentication paired with hardware keys is the gold standard for security this year.
Pillar III: Intelligent Patching and Zero-Day Response
Many of the major attacks in January exploited vulnerabilities for which patches had been available for months, but IT teams had delayed installation. Updating operating systems, management software, and security tools must be automated and daily. Every day of delay is a day of golden opportunity for hackers. For small businesses, this is the simplest and cheapest way to elevate security. Additionally, using automated monitoring tools that identify vulnerabilities as they emerge helps you stay one step ahead.
5. Security Culture: The Human Firewall
No matter how advanced the technology, the weakest link in the security chain is still the "human." The January attacks showed that social engineering remains the number one tool for hackers. Training employees to identify deepfakes, be skeptical of unexpected calls, and report unusual activities immediately can prevent massive disasters. Security must move from a technical topic to a shared priority at all levels of an organization.
Final Conclusion: Preparing for the Next Storm
January 2026 is just a preview of the decade ahead. The pace of attacks is increasing, and the tools available to attackers are becoming more powerful by the day. However, by being informed and using the defensive tools we discussed in these 2000 words, you can protect your digital assets. Tekin Plus is committed to being your partner on this journey. Always remember that security is not a destination, but a continuous path. With research, updates, and attention to detail, make 2026 a successful and secure year.
\n\n⚖️ نتیجهگیری معمار سیستم (Tekin Verdict)
بررسیهای عمیق دپارتمان تحقیقات ارتش تکین نشان میدهد که موضوع The Deadliest Cyber Attacks of 2026: A Deep Dive into Global Breaches صرفاً یک اتفاق گذرا نیست، بلکه تکه پازلی از یک تغییر معماری بزرگتر در صنعت تکنولوژی و سرگرمی است. ما در تکینگیم همواره این تحولات را زیر نظر داریم تا شما را در خط مقدم اخبار تحلیلی و بدون فیلتر نگه داریم.
